Conversation
|
Role |
f1c46d1 to
4d7e6aa
Compare
There was a problem hiding this comment.
Can we add parameters like --can-deleagate so that users can see help messages.
There was a problem hiding this comment.
Taking JSON as an input is asked by the service team. I had the same suggestion as you to expose explicit arguments but the suggestion was rejected.
There was a problem hiding this comment.
CLI is yours. You fix it. Be brave. Go ahead.
323363e to
2776a5f
Compare
| - name: Create role assignment for an assignee. | ||
| text: az role assignment create --assignee sp_name --role a_role | ||
| - name: Create role assignment for an assignee with description and condition. (Only for 2020-04-01-preview API version and later.) | ||
| text: >- |
There was a problem hiding this comment.
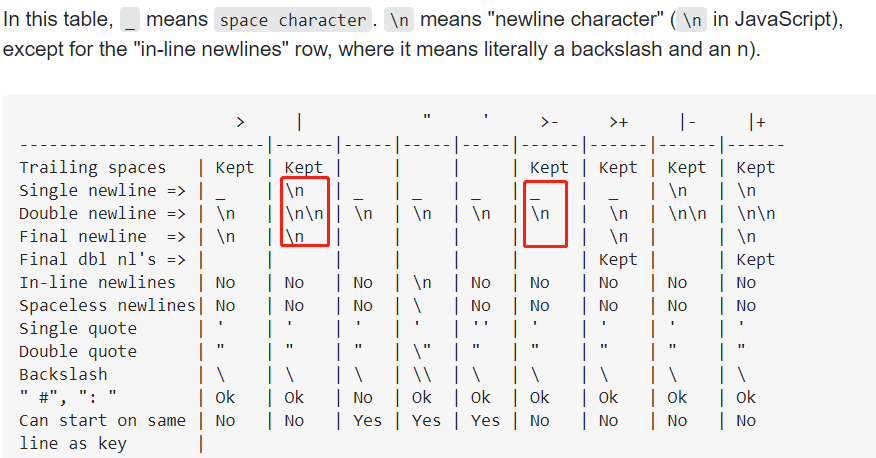
What's the difference between >- and |?
There was a problem hiding this comment.
@qwordy
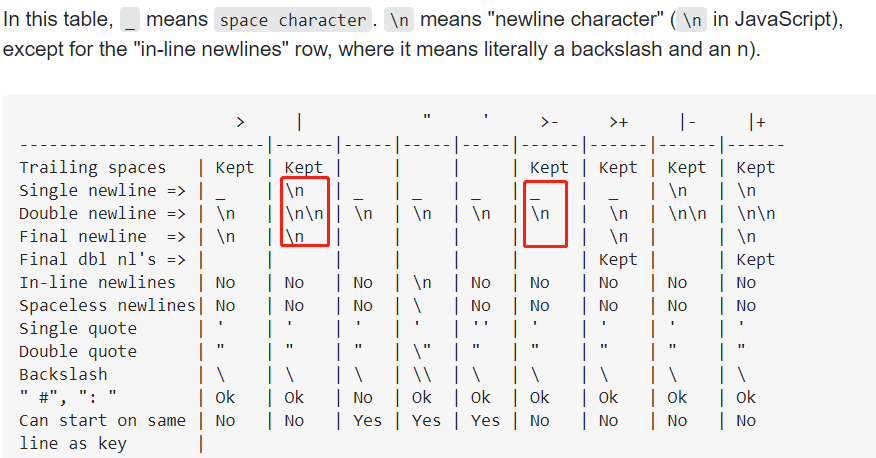
In short: >- will replace all single \n to whitespace (especially, the final \n will be removed), and combine double \n to one.
There was a problem hiding this comment.
I use >- to make the code more readable purposefully.
| - name: Create role assignment for an assignee. | ||
| text: az role assignment create --assignee sp_name --role a_role | ||
| - name: Create role assignment for an assignee with description and condition. (Only for 2020-04-01-preview API version and later.) | ||
| text: >- |
There was a problem hiding this comment.
@qwordy
In short: >- will replace all single \n to whitespace (especially, the final \n will be removed), and combine double \n to one.
| c.argument('include_classic_administrators', arg_type=get_three_state_flag(), help='list default role assignments for subscription classic administrators, aka co-admins') | ||
| c.argument('description', min_api='2020-04-01-preview', help='Description of role assignment.') | ||
| c.argument('condition', min_api='2020-04-01-preview', help='Condition under which the user can be granted permission.') | ||
| c.argument('condition_version', min_api='2020-04-01-preview', help='Version of the condition syntax. If --condition is specified without --condition-version, default to 2.0.') |
There was a problem hiding this comment.
How about adding this default value in the help message ?
Added. I didn't use the built-in default mechanism because it is a conditional default - only when --condition is specified.
Close #14552
az role assignment createDesign
New arguments to add to the existing arguments:
Examples
Sample Output:
{ "canDelegate": null, "condition": "@Resource[Microsoft.Storage/storageAccounts/blobServices/containers:Name] stringEquals 'foo'", "conditionVersion": "2.0", "description": "Role assignment foo to check on bar", "id": "/subscriptions/0b1f6471-1bf0-4dda-aec3-cb9272f09590/resourceGroups/rg1/providers/Microsoft.Authorization/roleAssignments/d89f022c-f12f-4fb5-9d90-afb9c1f4fd83", "name": "d89f022c-f12f-4fb5-9d90-afb9c1f4fd83", "principalId": "182c8534-f413-487c-91a3-7addc80e35d5", "principalType": "User", "resourceGroup": "rg1", "roleDefinitionId": "/subscriptions/0b1f6471-1bf0-4dda-aec3-cb9272f09590/providers/Microsoft.Authorization/roleDefinitions/acdd72a7-3385-48ef-bd42-f606fba81ae7", "scope": "/subscriptions/0b1f6471-1bf0-4dda-aec3-cb9272f09590/resourceGroups/rg1", "type": "Microsoft.Authorization/roleAssignments" }Checks
Description
descriptionis a string.descriptionis empty, replace with null.Condition
conditionis a string.conditionis empty replace with null.Condition-Version
condition-versionis a string.condition-versionmust be >1.0.The specified role assignment ConditionVersion '0.1' is not supported.condition-versionis empty andconditionis set,condition-versiondefaults to2.0.condition-versionis set,conditionmust be set as well.az role assignment updateDesign
Example
Sample Output:
{ "canDelegate": null, "condition": "@Resource[Microsoft.Storage/storageAccounts/blobServices/containers:Name] stringEquals 'foo'", "conditionVersion": "2.0", "description": "Role assignment foo to check on bar", "id": "/subscriptions/0b1f6471-1bf0-4dda-aec3-cb9272f09590/resourceGroups/rg1/providers/Microsoft.Authorization/roleAssignments/d89f022c-f12f-4fb5-9d90-afb9c1f4fd83", "name": "d89f022c-f12f-4fb5-9d90-afb9c1f4fd83", "principalId": "182c8534-f413-487c-91a3-7addc80e35d5", "principalType": "User", "resourceGroup": "rg1", "roleDefinitionId": "/subscriptions/0b1f6471-1bf0-4dda-aec3-cb9272f09590/providers/Microsoft.Authorization/roleDefinitions/acdd72a7-3385-48ef-bd42-f606fba81ae7", "scope": "/subscriptions/0b1f6471-1bf0-4dda-aec3-cb9272f09590/resourceGroups/rg1", "type": "Microsoft.Authorization/roleAssignments" }Checks
Same as for
role assignment createwith some small exceptions/additions:description,conditionandconditionVersioncan be modified.conditionVersioncannot be downgraded to1.X.Testing Guide