Feature/issue 278 verify signed messages#998
Conversation
 tomholub
left a comment
tomholub
left a comment
There was a problem hiding this comment.
Thanks! See details about how to understand the signature result.
FlowCrypt/Functionality/Mail Provider/Message Provider/MessageService.swift
Outdated
Show resolved
Hide resolved
|
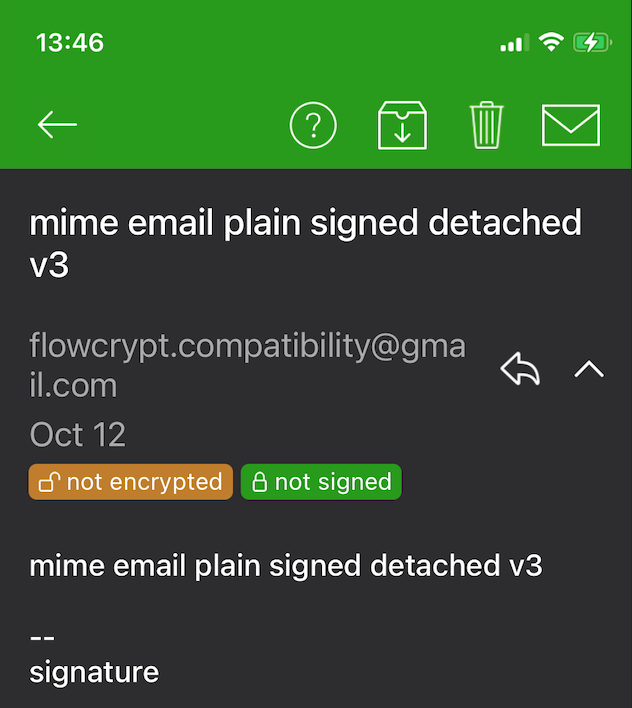
Rendering is well done - thank you. I gave you vague instructions but it turned out well 👍 just please put the green bubble below the date. Please have it say just Then please make sure it collapses together with the text when I collapse that message. Unless you think it shouldn't? |
|
And also let's do what you suggested: For plain emails it will show: for signed-only message it will show: etc |
Yes, I missed collapsing part, it definitely should collapse along with other message parts. |
FlowCrypt/Functionality/Mail Provider/Message Provider/MessageService.swift
Outdated
Show resolved
Hide resolved
FlowCrypt/Functionality/Mail Provider/Message Provider/MessageService.swift
Outdated
Show resolved
Hide resolved
FlowCrypt/Functionality/Mail Provider/Message Provider/MessageService.swift
Show resolved
Hide resolved
FlowCrypt/Functionality/Mail Provider/Message Provider/MessageService.swift
Outdated
Show resolved
Hide resolved
FlowCrypt/Functionality/Mail Provider/Message Provider/MessageService.swift
Outdated
Show resolved
Hide resolved
|
@tomholub I found an issue with non-encrypted messages here https://github.com/FlowCrypt/flowcrypt-ios/blob/feature/issue-278-verify-signed-messages/FlowCrypt/Functionality/Mail%20Provider/Message%20Provider/MessageService.swift#L168 In case when user receives plain non-encrypted mail then app tries to decrypt it, but can't find local pub keys for mail sender, so it sends request to Is there any method to find if message needs decryption or it's just plain text? |
Not reliably. This is why I was thinking to fetch the message from Gmail, and fetch the pubkey, in parallel. But fetching a public key from Attester can be even slower, especially when it's a 404 (and Attester itself is trying to fetch them from remote places). The proper way to do all of this, I think, is not to pre-fetch at all, but post-fetch and re-verify.
(btw - the chrome extension doesn't quite go as far at the moment. It renders the message, then realizes it's missing public key, fetches them, and if it finds any, renders "found a public key to verify this message, click here to verify). Clicking there just does |
# Conflicts: # FlowCrypt/Models/Realm Models/RecipientRealmObject.swift
 tomholub
left a comment
tomholub
left a comment
There was a problem hiding this comment.
Looking good from code - see comments
FlowCrypt/Controllers/Threads/ThreadDetailsViewController.swift
Outdated
Show resolved
Hide resolved
FlowCrypt/Controllers/Threads/ThreadDetailsViewController.swift
Outdated
Show resolved
Hide resolved
FlowCrypt/Controllers/Threads/ThreadDetailsViewController.swift
Outdated
Show resolved
Hide resolved
 tomholub
left a comment
tomholub
left a comment
There was a problem hiding this comment.
This looks good by code. What is the status of the PR - did you want to do more testing, or something left to do?
|
I want to test it with |
# Conflicts: # FlowCrypt/Controllers/Msg/MessageViewController.swift
I'll file another issue for it, not necessary to do now. |
| let signature: String | ||
| if let processedMessage = threadMessage.processedMessage, processedMessage.messageType == .encrypted { | ||
| signature = processedMessage.signature.message | ||
| } else { | ||
| signature = "message_not_signed".localized | ||
| } |
There was a problem hiding this comment.
This is likely the reason why signed-only messages are not recognized as signed - per above code, if they are not encrypted, they are always rendered as "not signed".
Would it be possible to always use processedMessage.signature.message regardless if encrypted or not? If that is missing, sounds like an error as well (since when signature is missing, processedMessage.signature.message is supposed to be there with notSigned case or similar)
Can address later.
There was a problem hiding this comment.
Yes, initially I thought that all signed messages are encrypted, and haven't implemented signature state check for this case.
There was a problem hiding this comment.
Check the browser extension - next to the send button, there is a chevron. That's how a signed-only message could be sent.
There was a problem hiding this comment.
Oh, didn't know about such feature 👍
This PR adds verification for signed messages
close #278
close #1021
Tests (delete all except exactly one):
MessageServiceTo be filled by reviewers
I have reviewed that this PR... (tick whichever items you personally focused on during this review):