UNIVERSITY OF WEST ATTICA
SCHOOL OF ENGINEERING
DEPARTMENT OF COMPUTER ENGINEERING AND INFORMATICS
University of West Attica · Department of Computer Engineering and Informatics
Information Technology Security
Vasileios Evangelos Athanasiou
Student ID: 19390005
Supervision
Supervisor: Ioanna Kantzavelou, Associate Professor
Co-supervisor: Angelos Georgoulas, Assistant Professor
Athens, April 2023
This project presents a comprehensive study of buffer overflow vulnerabilities. It combines theoretical analysis of memory management with a practical laboratory walkthrough demonstrating both exploitation and mitigation of stack-based buffer overflows.
The goal is to understand how buffer overflows occur, how they can be exploited in controlled environments, and how modern operating systems defend against them.
| Section | Path / File | Description |
|---|---|---|
| 1 | assign/ |
Official laboratory exercise specifications |
| 1.1 | assign/Exercise 1 (Buffer Overflow) - THEORETICAL PART.pdf |
Assignment description – theoretical part (English) |
| 1.2 | assign/Exercise 1 (Buffer Overflow) - PRACTICAL PART.pdf |
Assignment description – practical part (English) |
| 1.3 | assign/Άσκηση 1 (Buffer Overflow) - ΘΕΩΡΗΤΙΚΟ ΜΕΡΟΣ_2023.pdf |
Assignment description – theoretical part (Greek) |
| 1.4 | assign/Άσκηση 1 (Buffer Overflow) - ΠΡΑΚΤΙΚΟ ΜΕΡΟΣ_2023.pdf |
Assignment description – practical part (Greek) |
| 2 | docs/ |
Project reports and analysis |
| 2.1 | docs/Buffer-Overflow.pdf |
Technical report (English) |
| 2.2 | docs/Υπερχείλιση-Ενδιάμεσης-Μνήμης.pdf |
Technical report (Greek) |
| 3 | src/ |
Vulnerable programs and exploit source code |
| 3.1 | src/stack.c |
Vulnerable stack-based buffer overflow program |
| 3.2 | src/shellcode.c |
Shellcode implementation |
| 3.3 | src/dash_shellcode.c |
Shellcode adapted for dash shell |
| 3.4 | src/exploit.c |
Exploit construction and payload generation |
| 4 | figs/ |
Diagrams and theoretical illustrations |
| 5 | screens/ |
Experimental screenshots and attack validation |
| 5.1 | screens/Activity1–8/ |
Step-by-step evidence for each lab activity |
| 6 | README.md |
Project documentation |
| 7 | INSTALL.md |
Usage instructions |
The project analyzes how a program’s memory is organized and where vulnerabilities may arise:
- Text Segment: Stores executable program code.
- Data Segment: Stores initialized global and static variables.
- BSS Segment: Stores uninitialized global and static variables.
- Heap: Used for dynamic memory allocation (e.g.,
malloc()). - Stack: Stores local variables, function arguments, return addresses, and stack frames.
Each function call creates a stack frame containing:
- Function arguments
- Return Address
- Previous Frame Pointer
- Local variables
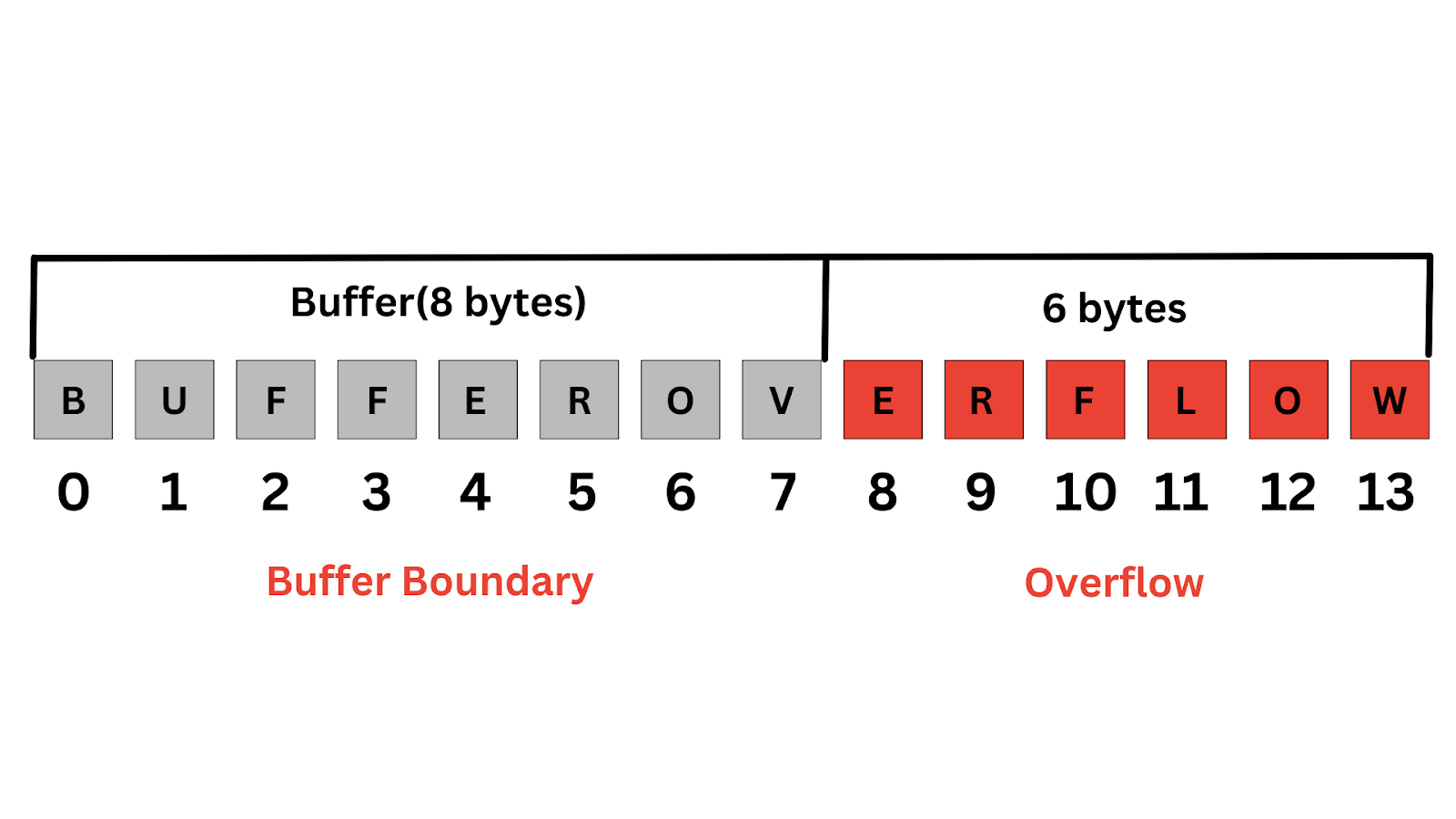
A buffer overflow occurs when a program writes more data to a buffer than it can hold.
In stack-based overflows, this can overwrite the Return Address, allowing an attacker to redirect execution to malicious code (shellcode).
The laboratory exercise demonstrates a buffer overflow attack in a controlled environment.
- ASLR disabled to make memory addresses predictable.
- A machine-level payload (
shellcode.c) was developed to execute/bin/sh, granting a command shell.
- A C program (
stack.c) was created using the unsafestrcpy()function, which does not perform bounds checking.
- An exploit utility (
exploit.c) generates abadfilecontaining:- NOP Sled: A sequence of
0x90instructions to increase exploit reliability. - Shellcode: The malicious payload.
- Modified Return Address: Redirects execution back into the buffer where the shellcode resides.
- NOP Sled: A sequence of
- By correctly calculating memory offsets and addresses, the exploit successfully redirected execution flow and spawned a shell with root privileges (
#).
The effectiveness of modern defenses was evaluated:
-
Stack Guard
- Detected stack corruption and terminated execution
- Error: “stack smashing detected”
-
Non-Executable Stack (NX)
- Prevented execution of stack-resident code
- Resulted in a Segmentation Fault instead of a shell
-
Address Space Layout Randomization (ASLR)
- Randomized memory addresses
- Made reliable exploitation significantly more difficult
This project demonstrates that buffer overflows remain a critical security threat, but modern operating system defenses, such as ASLR, Stack Guards, and Non-Executable Stacks, provide multiple layers of protection. While not foolproof individually, these mechanisms together greatly increase the complexity and difficulty of successful exploitation.