This is the list of projects completed in the 2025 programme.
- FakeMyVoice
- Train Your Foes
- Traffiq
- Voice2English
- Reinforcents
- Neural Quest
- Encrypted Chat Application
- Text to Handwritting
- EEG Analyser and Simulator
- MuseGan
- Multimodal Graph DB with RAG
- CodeSage
- Sera
- Kernel Design
- Cryptanalysis
- AI Ops
Fake My Voice is a deep learning-powered multi-speaker Text-to-Speech (TTS) system designed to clone voices with high fidelity. By extracting a unique 256-D speaker embedding from just a few seconds of reference audio, the pipeline replicates the specific tone, accent, and style of any target speaker.
The project integrates three state-of-the-art architectures:
- GE2E Encoder: Extracts robust vocal identity features.
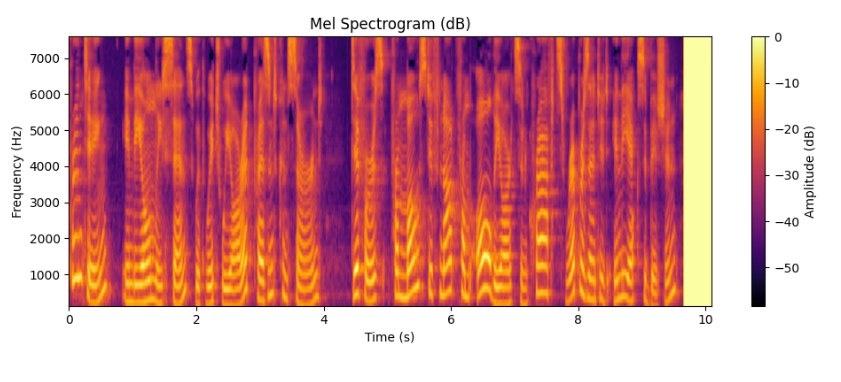
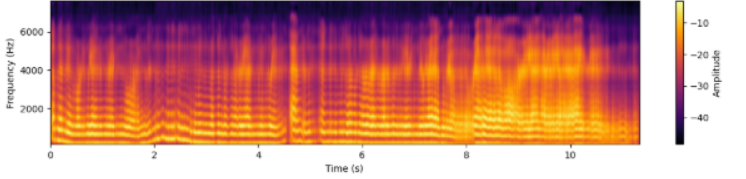
- Tacotron 2: Generates speaker-conditioned Mel-spectrograms from text.
- WaveGlow: A flow-based neural vocoder for natural waveform generation.
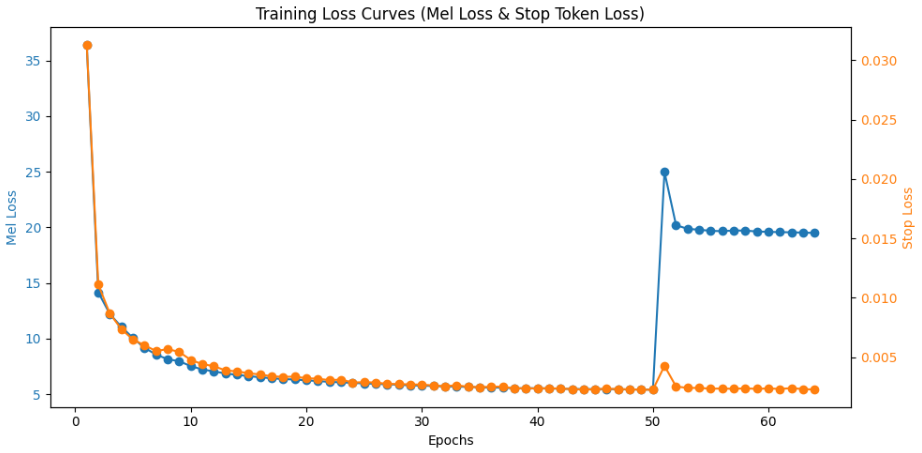
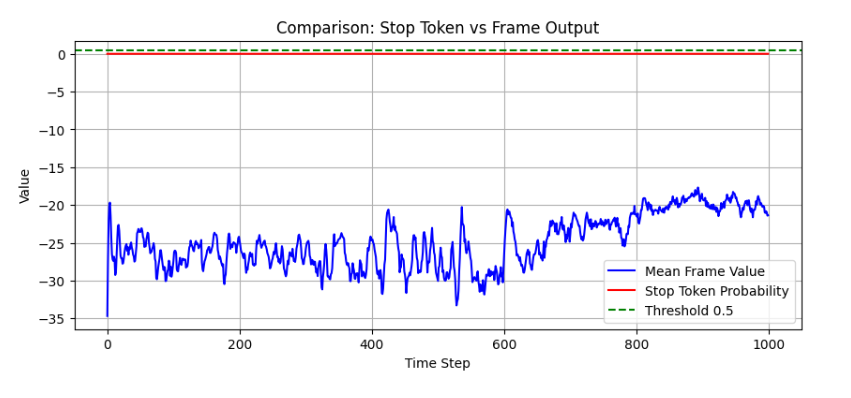
Achieved smooth Mel-spectrogram prediction after ~60 epochs.
Text: "Printing, in the only sense with which we are at present concerned"
| Expected Mel | Predicted Mel | Predicted Frames |
|---|---|---|
 |
 |
 |
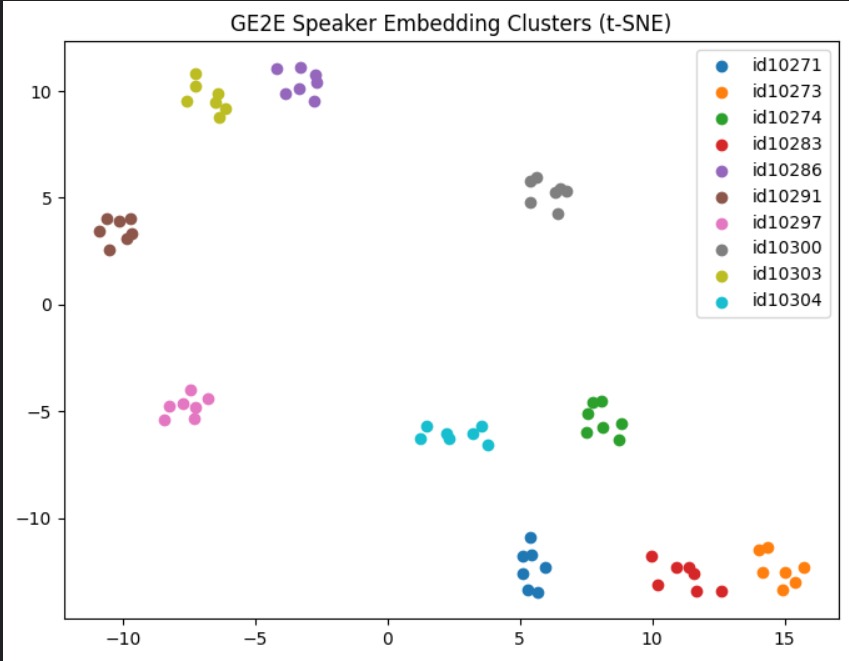
Achieved stable separation across 40+ speakers. t-SNE plots show distinct identity clustering.
- Mel Prediction: Mean Squared Error (MSE) Loss.
- Stop Token: Binary Cross-Entropy (BCE) Loss.
Download/Listen to Audio Sample
The audio says : "Use this model to clone the voice of any user"
- Source Code: FakeMyVoice-Project-X-2025
- Research Papers: Tacotron 2, GE2E Loss, WaveGlow.
- Datasets: LJSpeech, VoxCeleb, and VCTK Corpus.
- Implementation: NVIDIA Tacotron 2 + WaveGlow
Mentors:
- Kevin Shah
- Prasanna Kasar
- Yash Ogale
Domains: Deep Learning, Speech & Audio Signal Processing, Natural Language Processing (TTS)
Train Your Foes is a game where your greatest enemy is a machine that learns from you. Built in Unity 6, the game is split into two parts. First, you face The Gauntlet: four intense platforming levels that test your speed and precision. If you survive, you enter The Duel: a final boss fight that isn't scripted. Instead of following a set pattern, the boss uses Artificial Intelligence (Q-Learning) to study your health, energy, and moves. It chooses the best strategy to defeat you based on thousands of past battles, creating a unique challenge that feels alive and unpredictable.
1. Documentation: Full Documentation Site
2. Source Code: GitHub Repository
3. Engine: Unity Engine (6000.2.1f1)
4. Algorithm: Custom Q-Learning Implementation using the Bellman Equation:
Mentors:
• Abhay Varnekar
• Ishaan Shaikh
Domains: Game Development, Artificial Intelligence, Reinforcement Learning
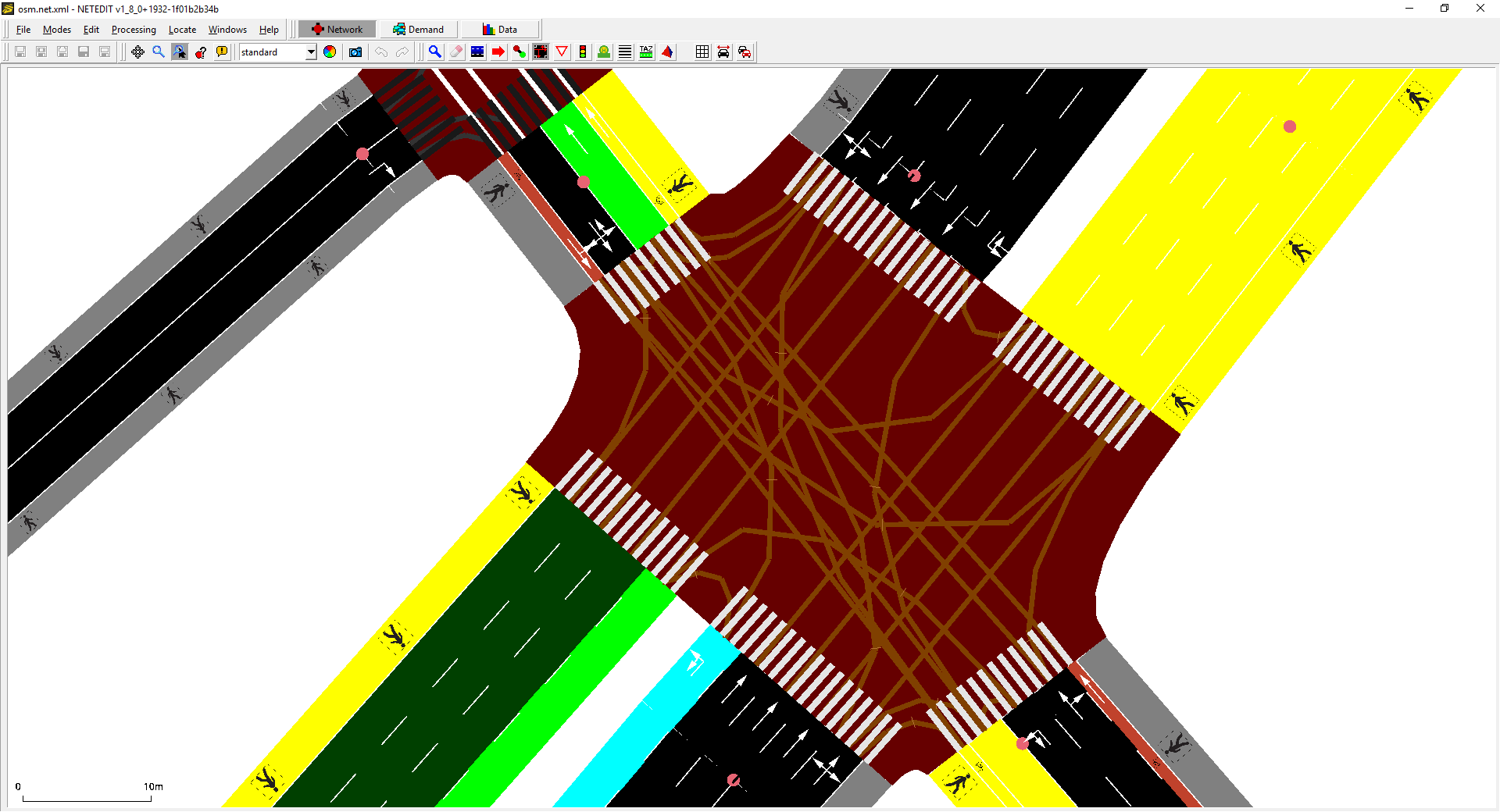
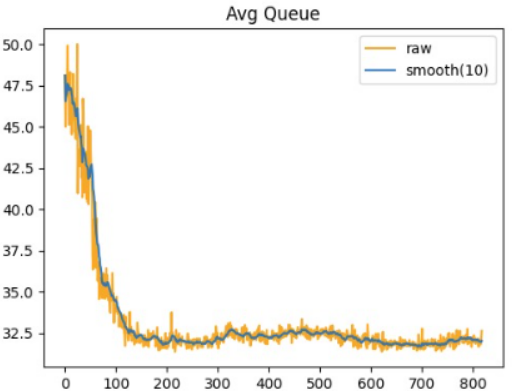
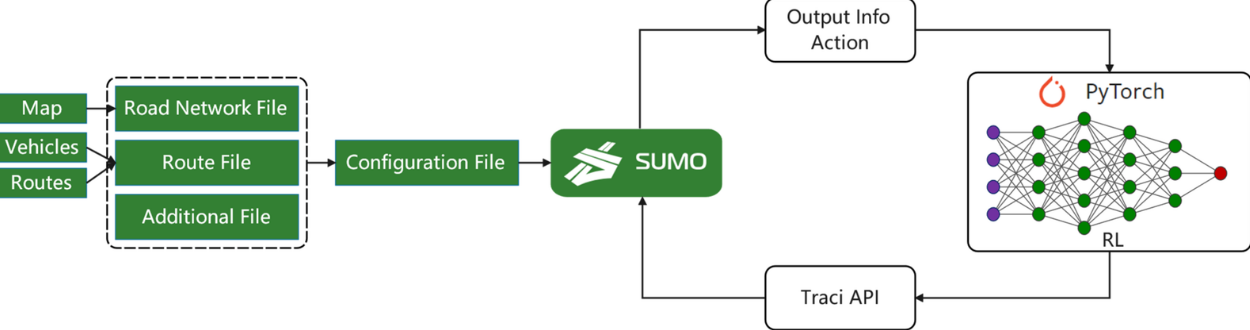
TrafIQ is an intelligent traffic signal control system that uses Deep Reinforcement Learning (DRL) to optimize signal timings in real-time. Built using SUMO simulation and algorithms such as Q-Learning, DQN, PPO, and MAPPO, the system dynamically adapts to traffic conditions to reduce queue lengths, waiting time, and emissions while maximizing throughput.
1. Documentation: Project Documentation
2. Source Code: GitHub Repository
3. Simulation Engine: SUMO (Simulation of Urban Mobility)
4. Frameworks: PyTorch, Gymnasium
Mentors:
- Yashvi Mehta
- Mahi Palimkar
Domains: Reinforcement Learning, Multi-Agent Systems, Intelligent Transportation Systems
Mentors:
Domains:
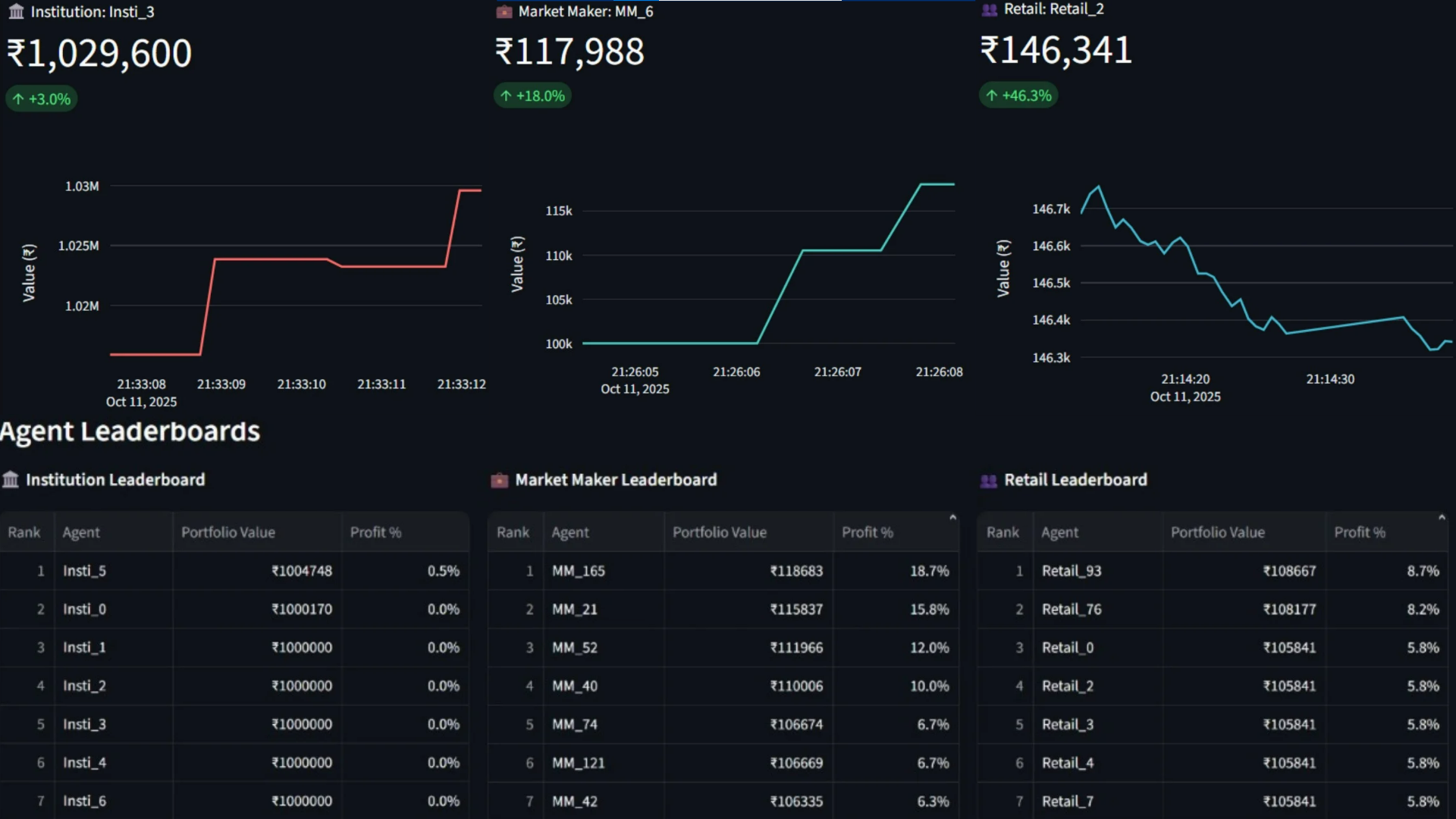
ReinforCents is a project that simulates a real-world stock and options trading market using Reinforcement Learning. It creates a virtual exchange where multiple intelligent agents interact and execute trades, similar to how trading happens in real financial markets.
The market is populated with three types of traders, each with unique behaviors and strategies:
- Market Makers: Provide liquidity by quoting bid/ask prices.
- Institutional Traders: Execute large, sophisticated, and long-term strategies.
- Retail Traders: Emulate the behavior of individual, often sentiment-driven, investors.
The system includes a working electronic exchange with a live order book, automatic trade matching, and real-time trade execution. The agents operate in this environment using advanced reinforcement learning algorithms, including:
- Soft Actor-Critic (SAC) for Market Makers
- Deep Deterministic Policy Gradient (DDPG) for Institutional Traders
Agents make decisions using financial modeling tools such as:
- Black-Scholes option pricing model
- Option Greeks (Delta, Gamma, Theta, Vega)
- Technical indicators (EMA, RSI, Stochastic Oscillator, ADX, CMF)
The project demonstrates how multiple AI agents can learn, compete, and make decisions within a simulated stock and options trading environment.
- Reinforcement Learning
- Soft Actor-Critic (SAC)
- Deep Deterministic Policy Gradient (DDPG)
- Options Trading
- Technical Indicators - EMA, RSI, Stochastic Oscillator, ADX, CMF
Mentors:
- Mudit Jain
- Krish Shah
Domains: Reinforcement Learning, Options Trading, Multi-Agent Systems
Mentors:
Domains:
Cryptify is a secure real-time messaging system built using Java Socket Programming and Spring Boot, designed to demonstrate low-level encrypted communication over TCP. The application implements Hybrid Cryptography, combining RSA (for secure key exchange) and AES (for fast symmetric message encryption) to ensure confidentiality and integrity. Messages are encrypted before transmission, securely exchanged over TCP sockets, and decrypted only by the intended recipient, ensuring that no plain-text data is exposed during communication.
1. Source Code: GitHub Repository
2. Documentation: Project Documentation
3. Encryption Standard: RSA-2048 for key exchange
4. Symmetric Encryption: AES-256 (GCM mode recommended)
5. Transport Protocol: TCP Socket Programming in Java
6. Security Model: Hybrid Encryption (RSA + AES)
Mentors:
• Rupak Gupta
• Tanish Bhamare
Domains: Cybersecurity, Network Programming, Cryptography, Secure Communication
This project generates realistic handwritten text from typed input using a Conditional Generative Adversarial Network (CGAN).
Unlike traditional handwriting synthesis systems that require large datasets or fixed vocabularies, this model learns writer-specific style from a small set of handwriting samples (approximately 15 images per writer).
A Content Encoder preserves textual correctness, while a Style Encoder captures unique handwriting characteristics. The Generator combines both representations to produce natural-looking handwritten word images.
The system produces handwritten word images that reflect:
- The provided input text
- Writer-specific stylistic features
- Natural handwriting variations
- GANwriting: Content-Conditioned Generation of Styled Handwritten Word Images
- IAM Handwriting Word Database
- Deep Learning Specialization — DeepLearning.AI
- Kaggle Datasets
Mentors:
Domains: Computer Vision, Generative Adversarial Networks (GANs), Natural Language Processing
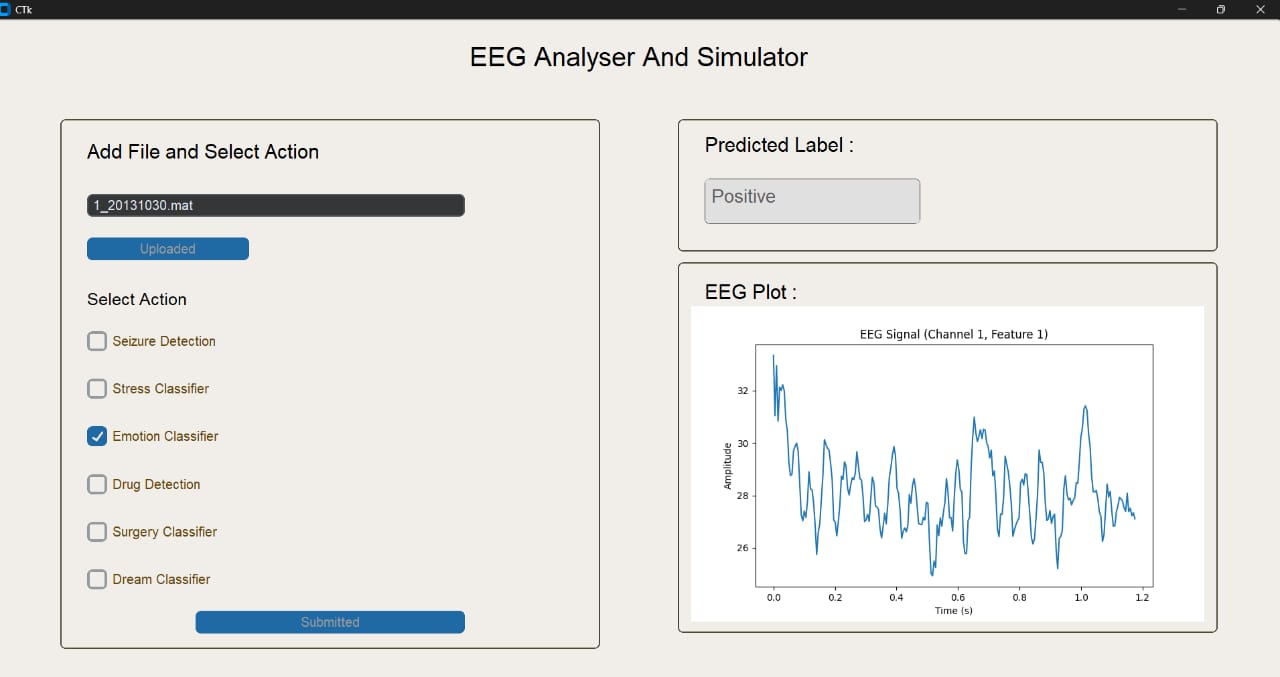
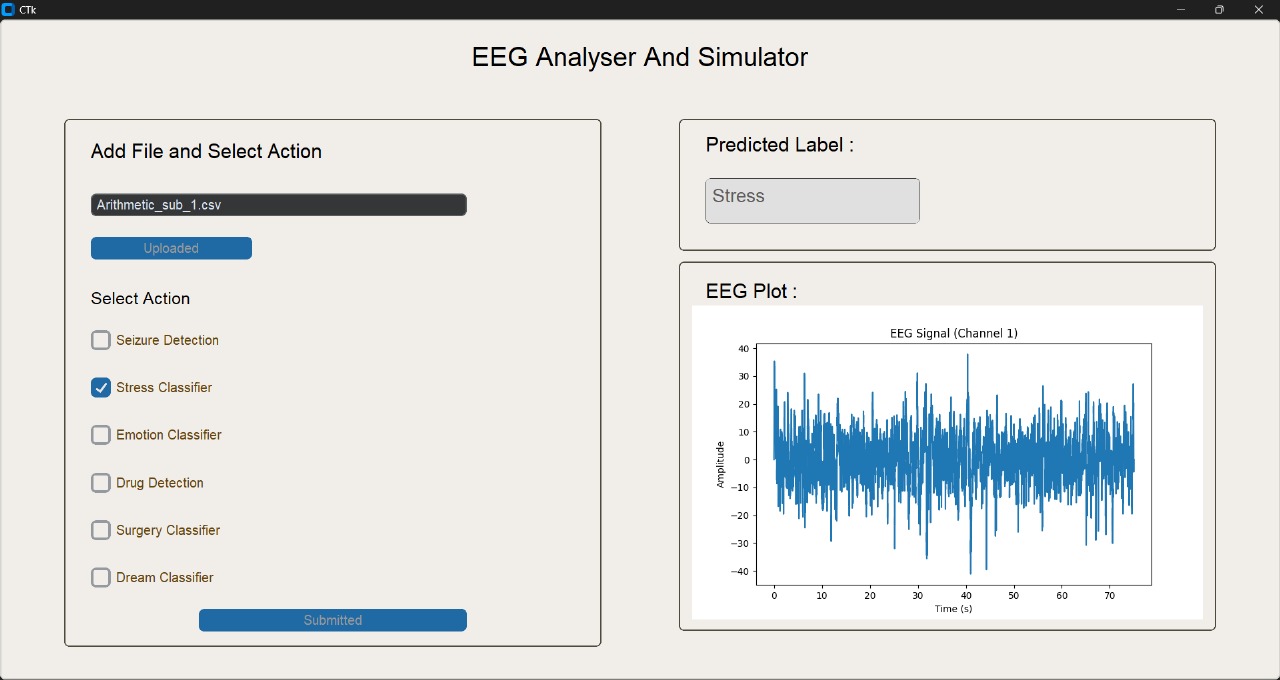
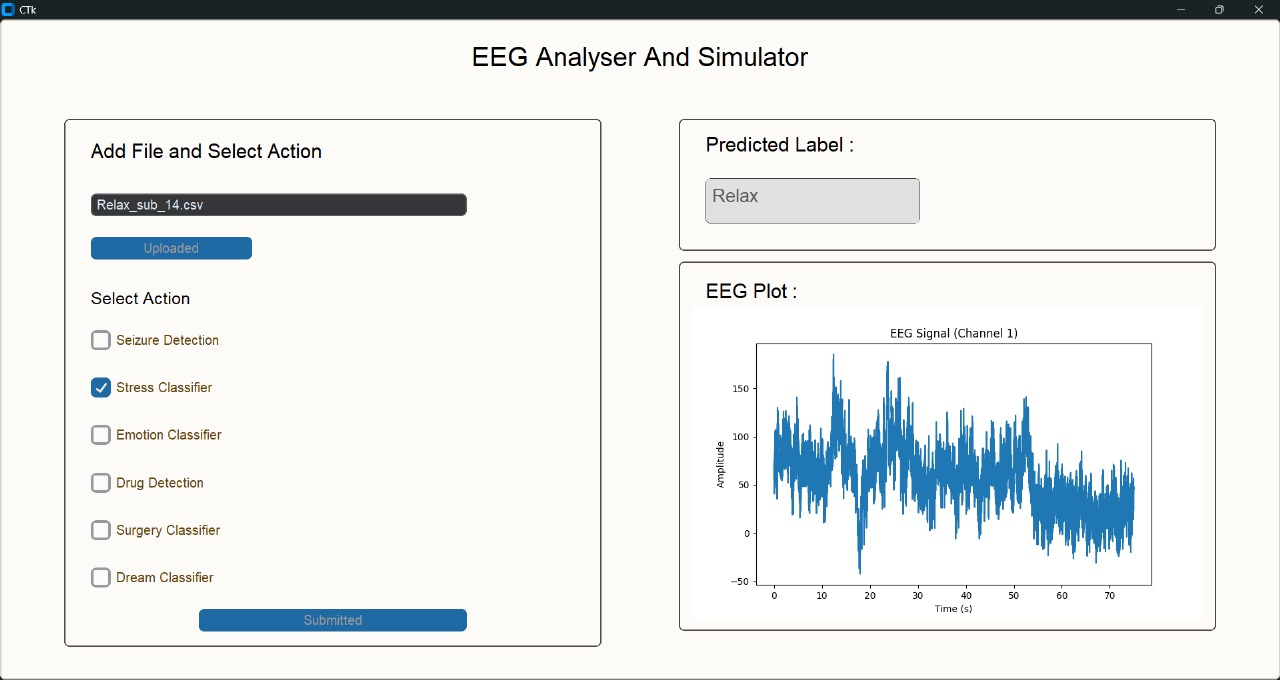
EEG Analyser and Simulator is a AI-driven simulation and prediction of brain dynamics using EEG data. This project aims to develop an AI-powered system that constructs a personalized Digital Twin of the Brain using EEG (Electroencephalogram) data. The system leverages deep learning and signal processing to analyze, predict, and simulate neurological patterns — enabling early detection of epilepsy, cognitive stress, depression, and other brain-related conditions. The system also aims to classify emotions in awake and dream phase. Other implications include the prediction of failure and success of surgery and drug identification and simulation of its effects on EEG data. In addition, the project explores neural generative modeling to interpret REM-phase brain activity into abstract visual representations, pushing the boundaries of dream analysis and subconscious understanding.
The system predicts the desired label for EEG signal and also plots it.
- Transformer paper
- Datasets:- SEED, TUH HUP, HUP iEEG, SAM40, DEED
- LSTM
- EEG SIGNAL PROCESSING
Mentors:
Domains: Signal processing, Machine Learning, Deep Learning
MuseGan is a GAN-based project for generating multi-track polyphonic music. It can generate coherent 4-bar music for 5 instruments from scratch and also supports Human-AI collaboration by conditionally generating tracks based on one human input track.
- Documentation: MuseGAN
- MuseGAN README: MuseGAN.md
- MuseGAN Repository: MuseGAN Repository
Mentors:
Domains: Music Generation, Generative Adversarial Networks (GANs), Temporal Sequence Modeling
Mentors:
Domains:
CodeSage is a Python-based framework that executes code and explains its logic in simple, human-readable language.
It combines compiler concepts with AI-based summarization to help users understand how code works internally.
- Lexer → Converts source code into tokens
- Parser → Builds an Abstract Syntax Tree (AST)
- Summarizer → Generates structured explanations
- Interpreter → Executes the AST (tree-walk)
- NLP (Optional) → Refines explanations
- GUI (Tkinter) → Editor, output, AST view, summaries
- Help students understand how interpreters work
- Explain code behavior clearly
- Visualize program structure
- Bridge programming with AI-based explanation
CodeSage runs code and explains it step-by-step.


Mentors: Yadnyesh Patil, Rupak Gupta
Domains: AST Parsing NLP
Mentors:
Domains:
Mentors:
Domains:
Cryptanalysis is a hybrid framework combining energy-based learning, side-channel analysis, and classical cryptography to analyze multiple ciphers. It first detects the cipher (AES, DES, Speck, or Vigenère), then applies an appropriate side-channel attack method with CNN-based key recovery for DES and Speck, statistical techniques for Vigenère, and only detection for AES due to its robustness. The system highlights how different ciphers require distinct attack strategies and demonstrates both practical vulnerabilities and modern security limits.




Mentors:
Domains: Side Channel Analysis, Energy-Based Models, Deep Learning, Cybersecurity, Classical Cryptography
Mentors:
Domains: