This report documents the capture and analysis of network traffic within a controlled lab environment to identify normal behavior and malicious activity from a Security Operations Center (SOC) perspective.
The analysis focused on:
- Baseline network behavior
- Port scanning reconnaissance
- SSH brute-force attack patterns
All findings were validated using packet-level inspection in Wireshark.
| Component | Details |
|---|---|
| Attacker | Kali Linux |
| Victim | Ubuntu Linux |
| Monitoring Tool | Wireshark |
| Virtualization | VMware Workstation (NAT) |
The investigation followed a standard SOC workflow:
- Establish baseline (normal traffic)
- Introduce suspicious activity
- Capture traffic
- Analyze packets
- Identify indicators of compromise (IOCs)
- Document findings and mitigations
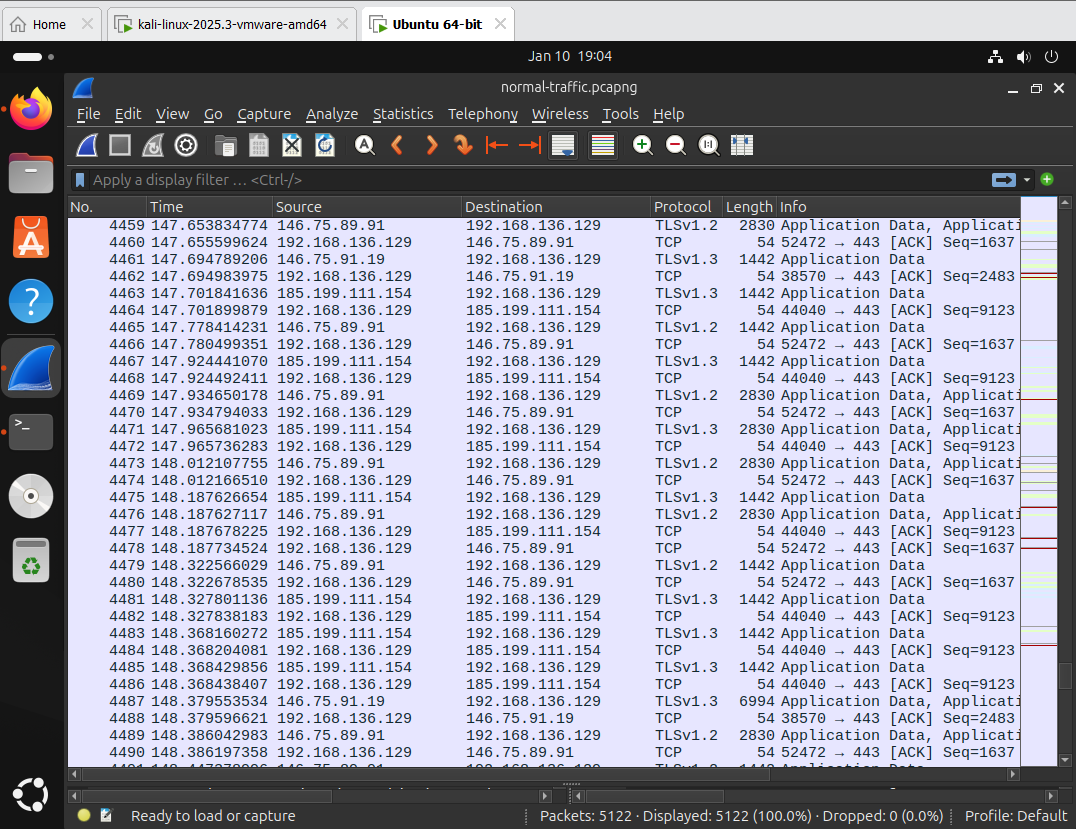
- ICMP echo requests (ping)
- Standard TCP handshakes
- Low packet volume
This traffic represents legitimate communication with no indicators of malicious intent.
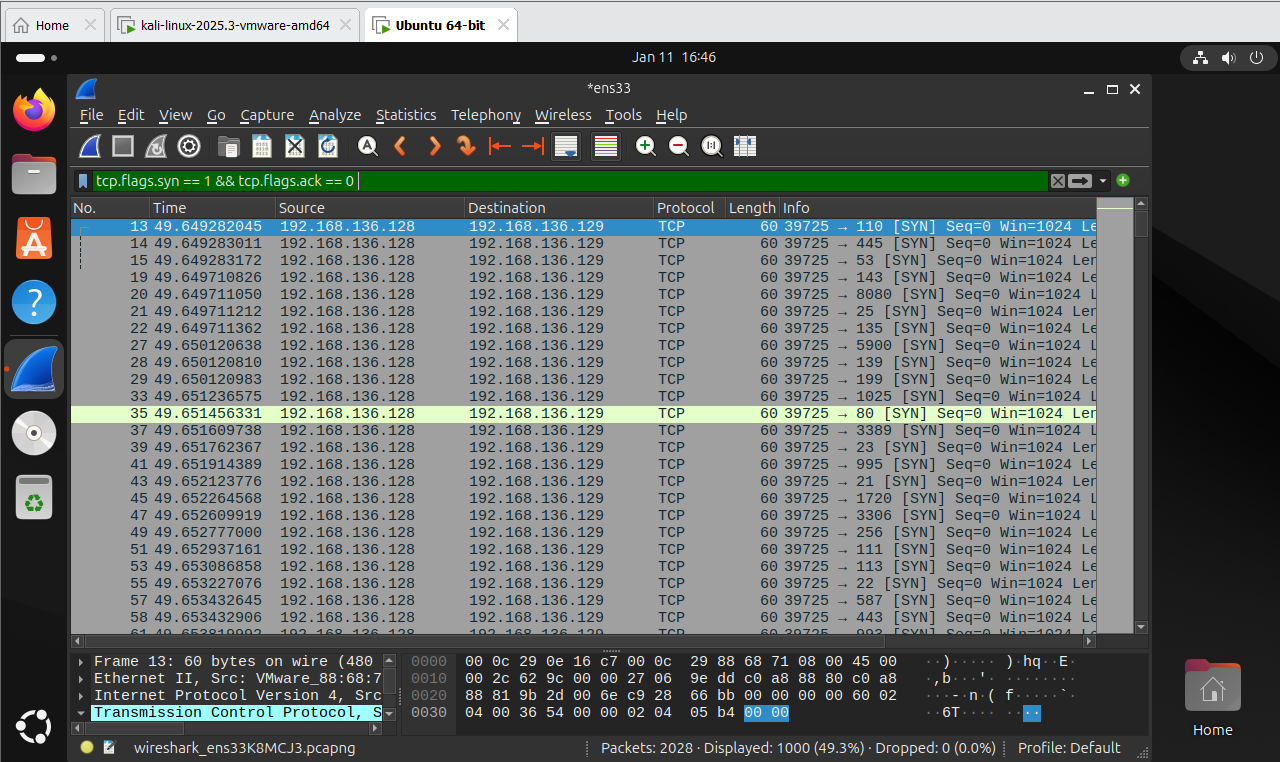
A TCP SYN scan was executed from the attacker machine to enumerate open services on the target system.
The traffic pattern clearly indicates reconnaissance activity commonly performed prior to exploitation.
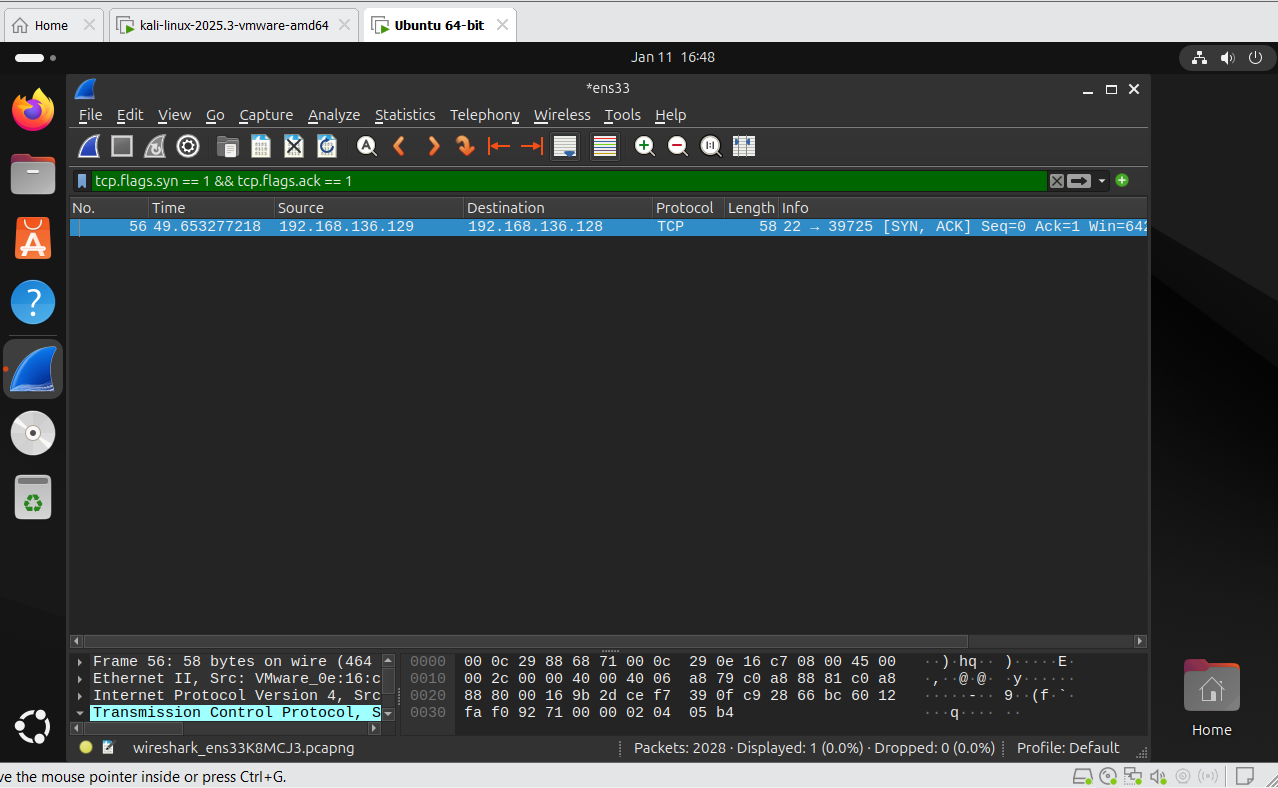
- Port 22 responded with SYN-ACK packets
- Confirms SSH service was actively listening
Open management ports significantly increase attack surface if not properly secured.
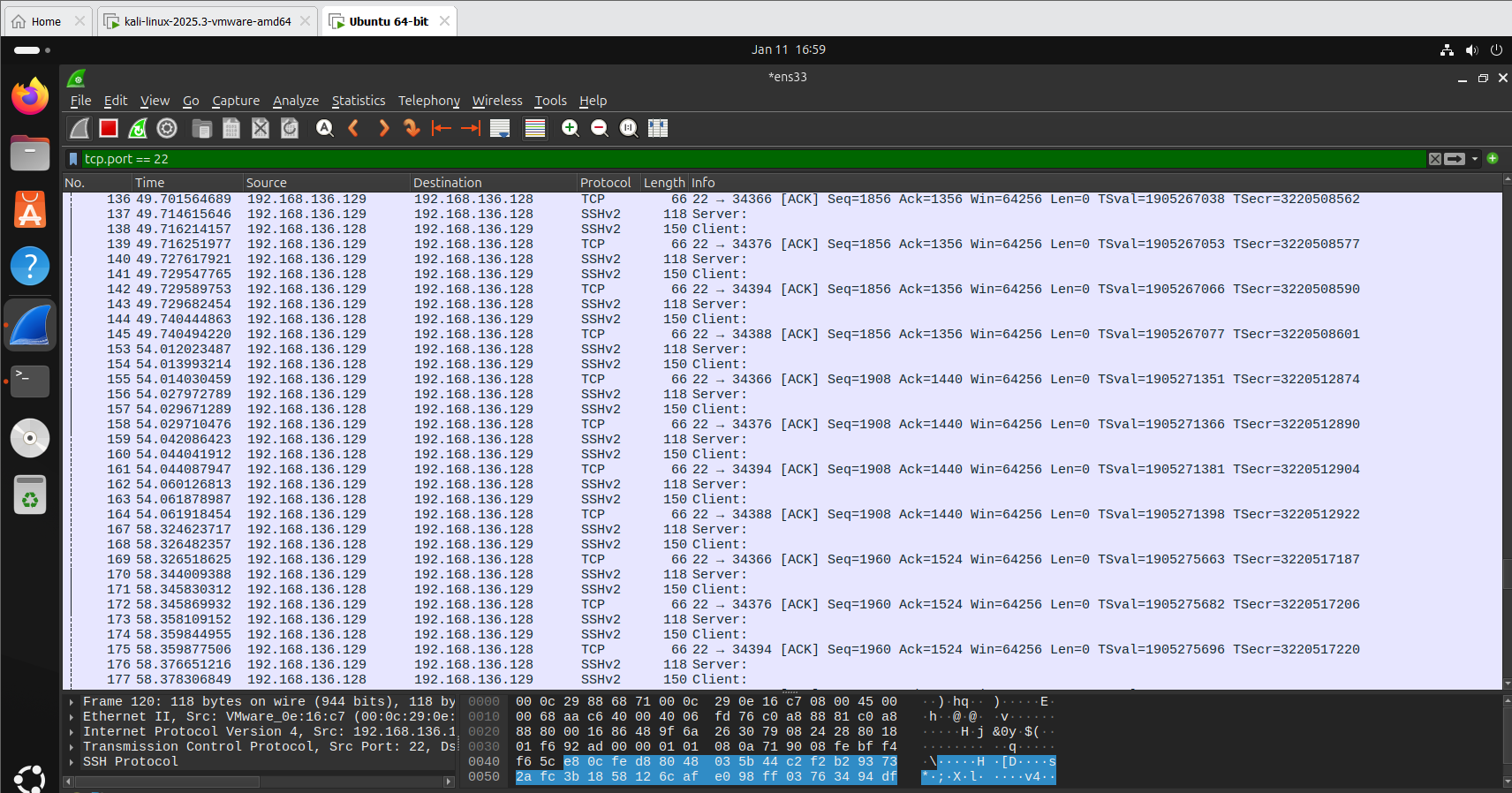
A brute-force login attempt was simulated against the SSH service.
- Repeated authentication attempts
- High-frequency SSH packets
- Single source IP targeting port 22
- Short time interval between attempts
tcp.flags.syn == 1 && tcp.flags.ack == 0
- Multiple SYN packets from a single source
- Sequential destination port probing
- Absence of completed TCP sessions
This activity strongly indicates a brute-force attack attempting to gain unauthorized access.
If successful, this attack could result in:
- Unauthorized system access
- Privilege escalation
- Lateral movement within a network
- Disable password-based SSH authentication
- Enforce SSH key-based authentication
- Implement rate-limiting tools (e.g., fail2ban)
- Restrict SSH access via firewall rules
- Continuous network traffic monitoring
This lab demonstrates the effectiveness of packet-level analysis in detecting early-stage and active attacks. The techniques used align with real-world SOC monitoring and incident investigation practices.
All activities were conducted in a controlled lab environment for educational purposes only.