Remove unnecessary randomize() call#5494
Remove unnecessary randomize() call#5494masaori335 wants to merge 1 commit intoapache:quic-latestfrom
Conversation
|
Those calls are probably from these two lines. trafficserver/iocore/net/QUICPacketHandler.cc Lines 98 to 99 in 9fc03ee I think we should probably have appropriate constructor and make |
|
They are wrong lines but the same thing. trafficserver/iocore/net/QUICPacketHandler.cc Lines 216 to 217 in 9fc03ee |
|
Also, |
I don't think trafficserver/iocore/net/quic/QUICTypes.cc Lines 559 to 563 in 9fc03ee |
|
|
|
That Update: I set breakpoint on randomize() and the line 289 is the first place which hit the breakpoint. |
|
OK, then we should be able to make it Which case is more common? |
|
My preference is not having public randomize(), and having constructors for each use cases. |
|
It could be another option, but which means when somebody just declare |
|
Is it better than use of non-randomized value at where it has to be? |
|
In this case the ConnectionId doesn't have to be randomized nor ZERO. It's just declared. |
|
After discussion of default constructor design of QUICConnectionId (performance vs security) on slack, we decided to push workaround fix (initializing with ZERO) for now. 4aa5ba2 |
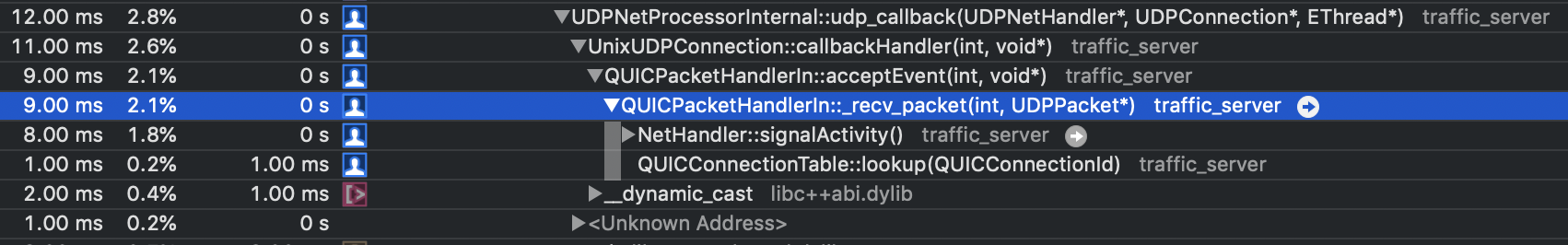
QUICConnectionId::randomize()is always called byQUICPacketHandlerIn::_recv_packet()from here.trafficserver/iocore/net/QUICPacketHandler.cc
Line 289 in 08042e6
This looks bit expensive.
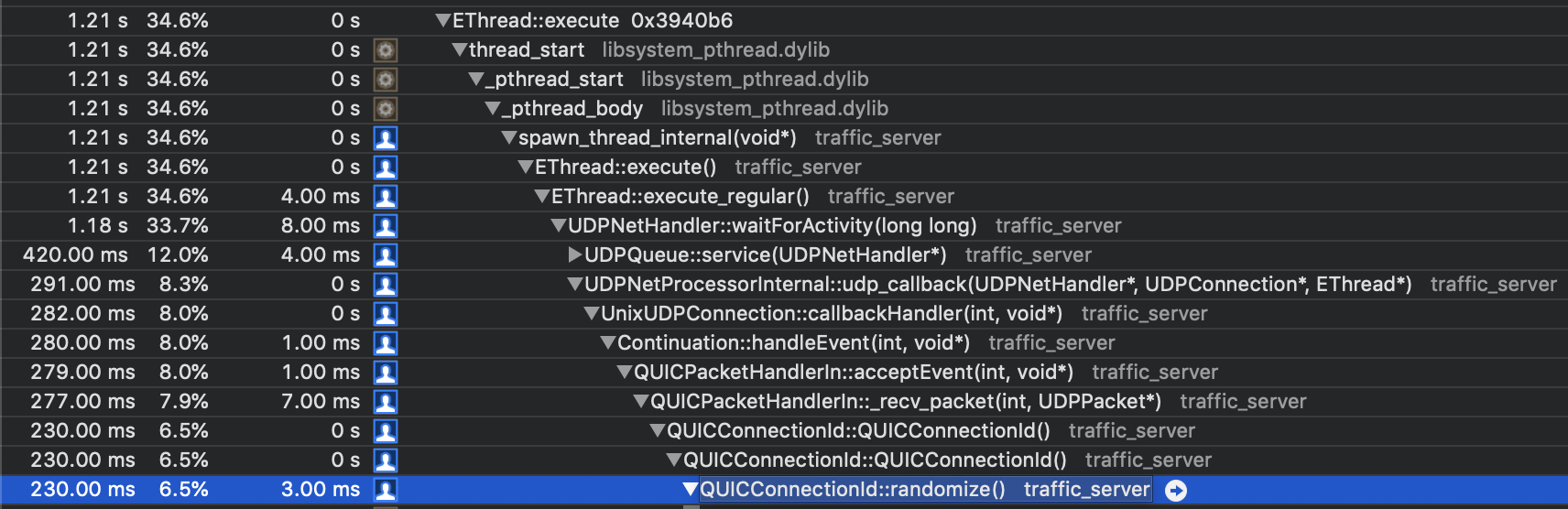
It looks like
QUICConnectionId::randomize()is called explicitly when it is needed. Is there any place assuming randomizing is done in constructor?