[JENKINS-54126] if strange 404 when cache is on #204
Conversation
| //JENKINS-54126 try again without cache headers | ||
| final Connector.ForceValidationOkHttpConnector oldConnector = (Connector.ForceValidationOkHttpConnector) gitHub.getConnector(); | ||
| try { | ||
| //TODO I'm not sure we are alone in using this connector so maybe concurrent modification problems |
There was a problem hiding this comment.
maybe have a withoutCache method that takes a closure, that way you could use a lock in the connector to ensure the correct one gets used... if you are worried about concurrent requests
 stephenc
left a comment
stephenc
left a comment
There was a problem hiding this comment.
I think we're going to have to accept this kind of hacks until we find the root cause.
May want to have a system property to turn off if cutting a release
| } | ||
| // means that does not exist and this is handled below this try/catch block. | ||
| } | ||
| if (finicky) { |
There was a problem hiding this comment.
if (finicky && !Boolean.getBoolean("disable hack")) { (or better an effectively final field) so that if your finicky hack is causing issues in production you can at least turn it off without restarting
|
I've been staring at that spotcheck error and it doesn't make sense to me, it seems like something obvious but I can't see it. |
| // means that does not exist and this is handled below this try/catch block. | ||
| } | ||
| if (finicky) { | ||
| final Optional<List<String>> status = Optional.ofNullable(fnf.getResponseHeaderFields() != null ? fnf.getResponseHeaderFields().get(null) : null); |
There was a problem hiding this comment.
I think you are not supposed to pass an explicit null to Optional.ofNullable... so try
fnf.getResponseHeaderFields() != null ? Optional.ofNullable(fnf.getResponseHeaderFields().get(null)) : Optional.empty())
Or perhaps it is the .get(null) that it objects to @rsandell
|
To help set context for the strange looking 404 errors, a little back story on the tests I've been running. The relationship between strange 404s and missing branches/PRs
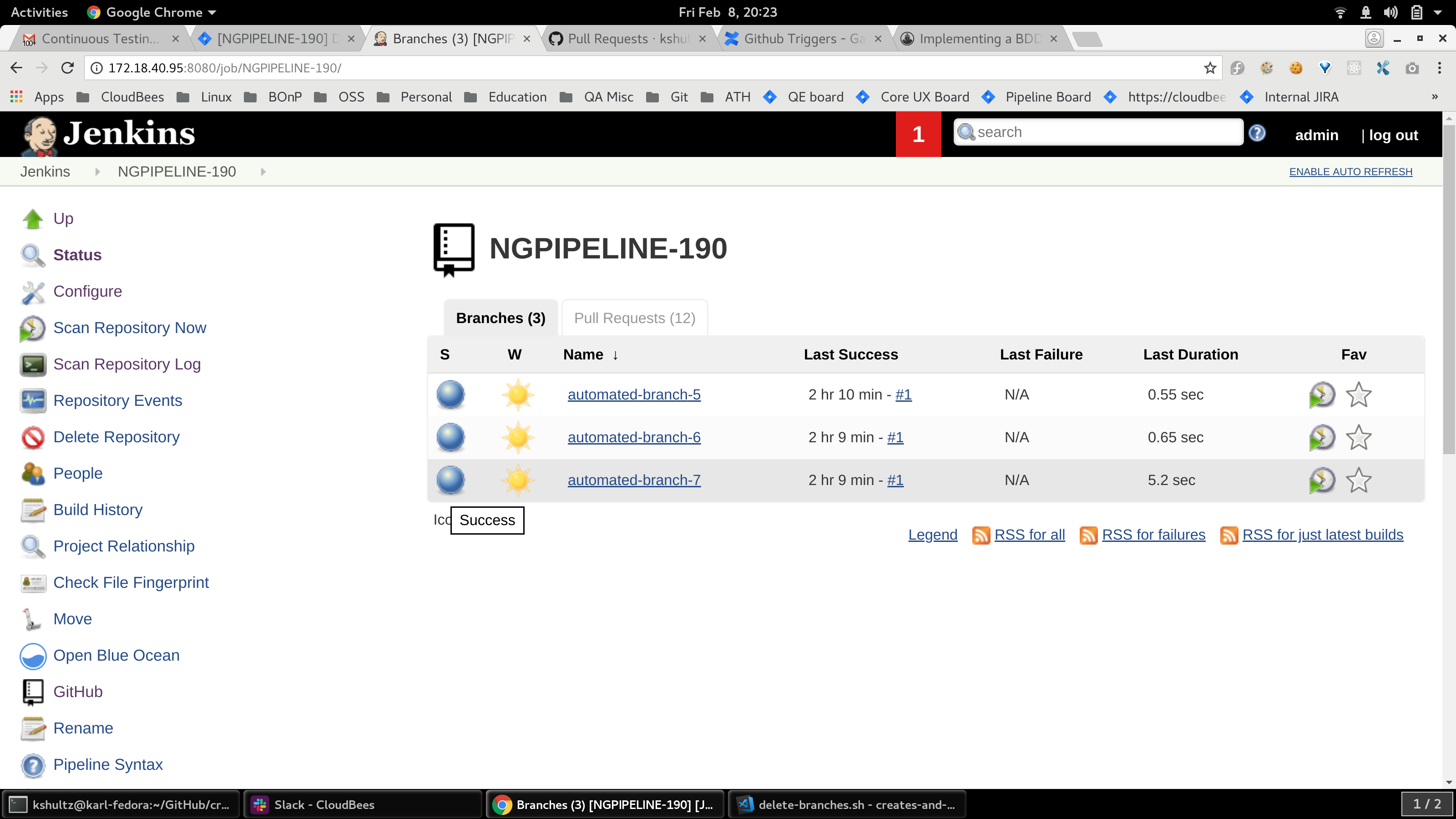
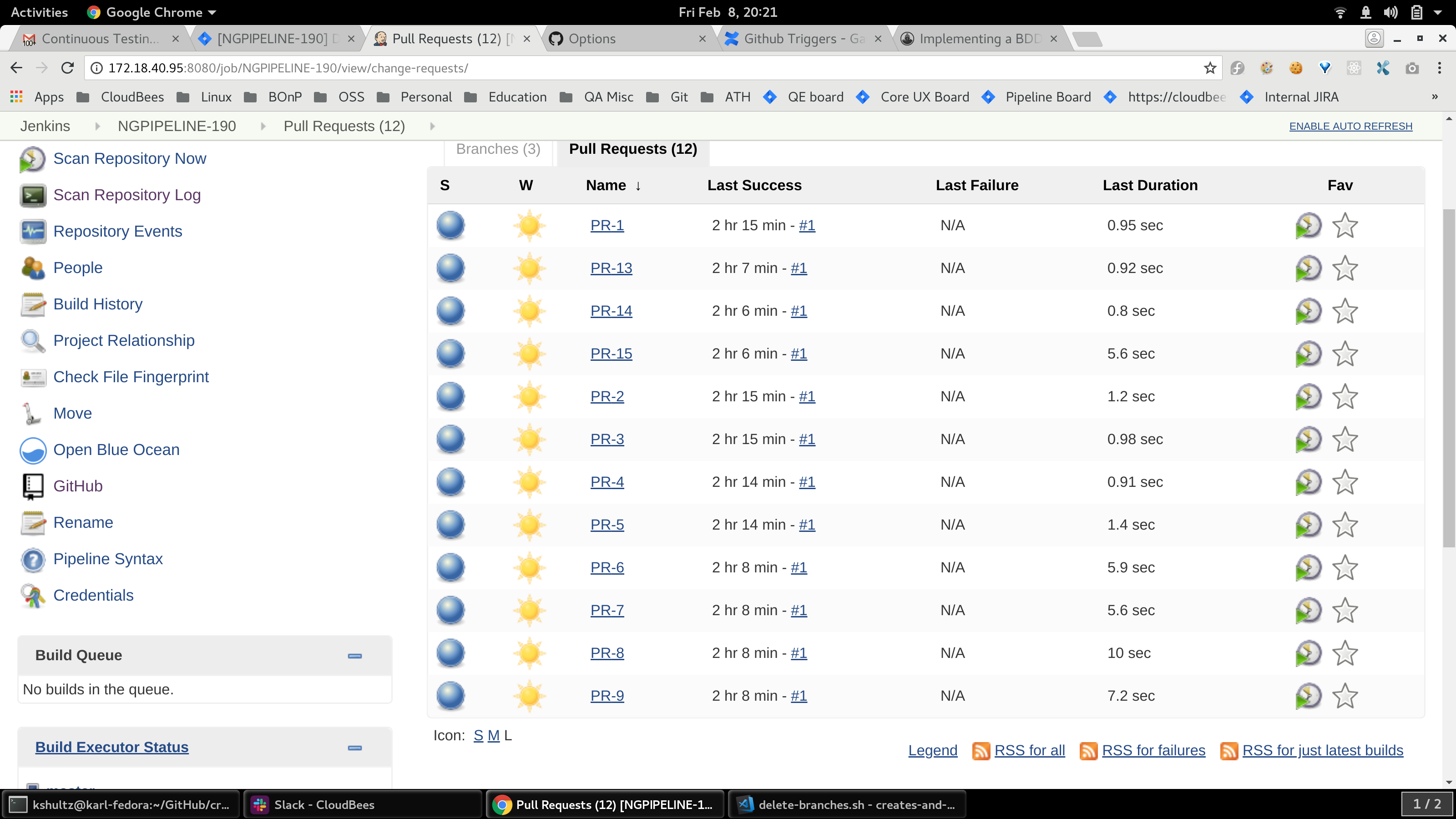
Only when this 404 was present during a branch create operation did I see inconsistent behavior from Jenkins. But, importantly, I have seen a direct relationship between the 404s and the inconsistent Jenkins behavior. If GitHub does not report a 404, everything works fine. But if it does, the inconsistent branches and PRs would appear in Jenkins, every time. That inconsistent behavior looks like:
How are things going with this PR in place
|
| // means that does not exist and this is handled below this try/catch block. | ||
| } | ||
| if (finicky) { | ||
| final Optional<List<String>> status = Optional.ofNullable(fnf.getResponseHeaderFields() != null ? fnf.getResponseHeaderFields().get(null) : null); |
There was a problem hiding this comment.
| final Optional<List<String>> status = Optional.ofNullable(fnf.getResponseHeaderFields() != null ? fnf.getResponseHeaderFields().get(null) : null); | |
| final Optional<List<String>> status = Optional.ofNullable(fnf.getResponseHeaderFields() != null ? Optional.ofNullable(fnf.getResponseHeaderFields().get(null)) : Optional.empty()); |
Turning @stephenc 's comment into a suggestion.
There was a problem hiding this comment.
That didn't help. It was because it thought that just because the method didn't return null on the first call it could on the second call 🤦♂️ .
|
@rsandell - With the cache turned on Jenkins fetches the repo and then get that specific Jenkinsfile at a particular revision, right? @kshultzCB - So what you're saying is we don't have a stable recreate of the issue using the unmodified plugin? |
|
@bitwiseman - I'm saying "on Monday, we had a fairly reliable recreate. And now, I got nothin'." :( Not a single recreate with the unmodified plugin since Tuesday afternoon, and I've done it hundreds of times. I did reach out to GitHub themselves about the issue. They pointed me to a couple of Stack Overflow articles (1, 2), both of which talk about okhttp being at fault for the gibberish characters. I got curious and started poking around. The version of okhttp that's in use by More poking around showed me that, if that is indeed the issue (or even just part of the issue), it's probably not a simple drop-in operation to update okhttp in |
|
The initial feature of cache i added in github-plugin, but with this ancient libraries better disable it. The correct solution will be to start using fresh library and excluding cache for some error codes. |
|
@kshultzCB |
|
Yep, I helped out with Java-8-i-zation of gerrit-trigger, so I thought, maybe I could at least take a quick look. Didn't get much further along than that. Thinking out loud: would it make sense to have the cache be opt-in? That's already been done for Windows because of a file naming problem. If it were opt-in, users could make a decision based on their needs. If they're hitting a lot of rate limit problems, they could turn it on, knowing there might be some tradeoffs. Maybe that might be a decent stopgap measure until some modernization can be done (Java8, okhttp3, etc). |
|
I've already bumped this plugin to Java 8 (hence the use of |
|
The one I was looking at that's not yet been bumped to Java 8 was github-plugin. |
|
Since the problem on the GitHub side seems to have magically disappeared during the last two weeks. Maybe we should merge this with the feature flag off by default? |
temporarily turn it off and try again