{VM} Fix #14897: display all requirements for vm admin password when it's invalid#14902
Conversation
| if len(password) not in range(min_length, max_length + 1): | ||
| raise CLIError('The password length must be between {} and {}'.format(min_length, | ||
| max_length)) | ||
| raise CLIError("Your password is invalid for it violates Rule 1\n{}".format(error_msg)) |
There was a problem hiding this comment.
LGTM. why not make it simpler. error_msg = Password length must be between {} and {}, and must have the 3 of following....". In CLIError, just message "Your password doesn't meet requirement, pls see password constraint: {}".format(error_msg)
There was a problem hiding this comment.
I think user knows where is error better when we split the error cases.
There was a problem hiding this comment.
Maybe we can just show the rule that the user violates instead of printing all rules.
|
thanks for quick fix! |
|
/azp run |
|
Azure Pipelines successfully started running 2 pipeline(s). |
| # pylint: disable=line-too-long | ||
| if count < 3: | ||
| raise CLIError('Password must have the 3 of the following: 1 lower case character, 1 upper case character, 1 number and 1 special character') | ||
| raise CLIError("Your password is invalid for it violates Rule 2\n{}".format(error_msg)) |
There was a problem hiding this comment.
Maybe we can just show the rule that the user violates instead of printing all rules.
There was a problem hiding this comment.
That's exactly what the issue was open for. They want to know all the rules once they failed :(
There was a problem hiding this comment.
I suggest create a survey to collect users' opinions widely. That's just one user's appeal.
There was a problem hiding this comment.
Our PM opened this issue, I think she knows the users well ~
|
Thank you all for the great discussion! Was informed of this new issue and thought I could leave a note to help clarify the ask: The system logic @qwordy laid out makes sense and I like how it also aligns with portal's. If we're merely checking whether the user PWD has passed certain criterion from the CLI side then there's no fault in checking those conditions one by one. However from the user perspective we should make clear of all the PWD requirements once they encounter the error to provide guidance and to prevent additional UX papercuts Here's the scenario --- suppose Bob is looking to set the admin password for his new VM with a short password only to encounter the "the password length must be between 12 and 123" error. When he sees that, he'd only attempt to lengthen the password since he's unaware of any other PWD requirements. Little did he know that he will actually fail once more because the new PWD is highly likely not complicated enough. So in this case, there's a very high chance that Bob (and hundreds others like Bob) has to spend 2x time to come up with an appropriate and acceptable password But if we make all the PWD requirements clear from the very beginning, then Bob can take into account all of those when coming up with an appropriate password once he hits the initial error So I'm perfectly content if we: i) only show the "password too short" error if the password is too short but is complicated enough; The original request maps to iii) above Hope the context makes sense... |
|
👍 💯 👍 |
|
I agree with showing all the rules to user from the very beginning. Actually the user experiences are different between portal and CLI, so I think we do not need to follow portal's behavior. However the "Rule 1, Rule 2" message seems a little imperative, suggest to combine them together and make it more friendly. |
|
Thanks everyone! With these discussions, I think the behavior here is what we agree on |
what's the difference between this one and original issue? I agree with @chenlomis as a client tool it's better to show the constraint to user completely. On portal, it's very easy to show it with UI, user types something, the error shows immediately. while in Azure CLI, user need to run command repeatedly to get all rules. |
|
Current help message for |
|
So, let's conclude the discussion. Whenever user inputs an invalid password, we will show the error message below. |
Description
This PR fix issue #14897.
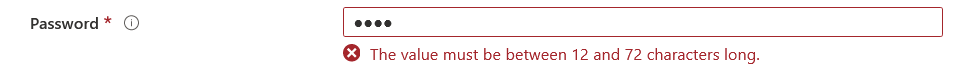
Before
When creating a vm with an invalid admin password, the message shows only the current rule the password violates. When user changes the password and try it again, another error may happen showing that the user violates anthoer rule.
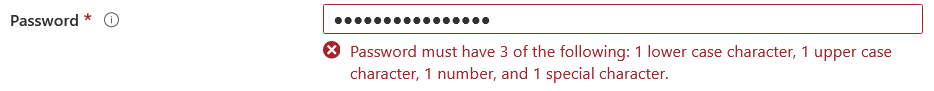
After
This PR improves the behavior by displaying all the requirements once we found the password is invalid.
Testing Guide
Before
After