Require DATASOURCE WRITE access in SupervisorResourceFilter and TaskResourceFilter#11680
Conversation
|
@kfaraz Is it possible to add integration tests that call all the different endpoints that are available on the ingest path and validate that a user needs DATASOURCE WRITE permission to see . I skimmed the code and noticed users with DATASOURCE READ can see metadata about the segments. I think this seems ok since a DATASOURCE READ user may need to know which segments were available when a query was executed so they would have a need. I dug a little bit and it seems like the segment metadata could include the loadSpec. Do you think that should also require DATASOURCE WRITE permissions? |
 suneet-s
left a comment
suneet-s
left a comment
There was a problem hiding this comment.
This change LGTM with 2 comments
- Can we add integration tests - maybe piggybacking off some of the security based integration tests?
- What should we do about segment metadata - should that require DATASOURCE WRITE?
Neither of these comments are blockers to this PR, so I'm approving the PR - but we might want fast follow ups to address these points
|
Thanks for the review, @suneet-s . I will add an integration test in a follow up PR (hopefully within a couple of days). I will also spend some time on the access of segment metadata and propose required changes, if any. |
…esourceFilter (apache#11680) * Require DATASOURCE WRITE access in SupervisorResourceFilter and TaskResourceFilter * Remove unused imports * Add SupervisorResourceFilterTest * Verify mocks in test
|
I missed a couple of things in my initial review, SQL queries to sys.tasks and sys.supervisors still use read permissions and a handful of task report APIs also still use read instead of write so this change isn't quite yet complete I think. (I do still think WRITE makes more sense for the changes here and all of these APIs). I'm not sure if I missed any others, probably worth having another look. |
|
Thanks for checking, @clintropolis . I am taking another pass at the APIs and will share the results of my findings here. |
|
Removed milestone |
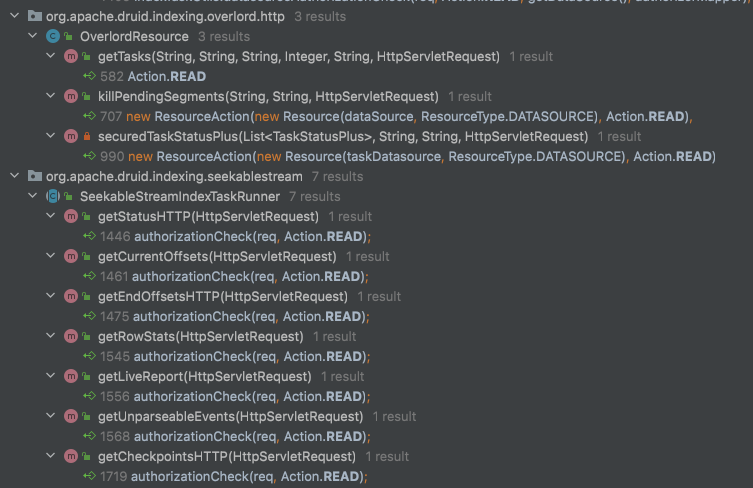
…#11718) Follow up PR for #11680 Description Supervisor and Task APIs are related to ingestion and must always require Datasource WRITE authorization even if they are purely informative. Changes Check Datasource WRITE in SystemSchema for tables "supervisors" and "tasks" Check Datasource WRITE for APIs /supervisor/history and /supervisor/{id}/history Check Datasource for all Indexing Task APIs
…nd TaskResourceFilter (apache#11680)" This reverts commit 6779c46.
* Revert "Require Datasource WRITE authorization for Supervisor and Task access (#11718)" This reverts commit f2d6100. * Revert "Require DATASOURCE WRITE access in SupervisorResourceFilter and TaskResourceFilter (#11680)" This reverts commit 6779c46. * Fix docs for the reverted commits * Fix and restore deleted tests * Fix and restore SystemSchemaTest
…nd TaskResourceFilter (apache#11680)" This reverts commit 6779c46.

Description
Users with DATASOURCE READ access can currently call GET and HEAD APIs
on Supervisor and Task resources. These resources respond with ingestion related
information, which should be visible only to DATASOURCE WRITE users.
Changes
SupervisorResourceFilterandTaskResourceFilterThis PR has: