Add basic security functions to druidapi#14009
Closed
paul-rogers wants to merge 4 commits intoapache:masterfrom
Closed
Add basic security functions to druidapi#14009paul-rogers wants to merge 4 commits intoapache:masterfrom
paul-rogers wants to merge 4 commits intoapache:masterfrom
Conversation
vtlim
reviewed
Apr 3, 2023
Contributor
Author
|
@vtlim, thanks again for acting as my spell-checker and proof-reader! |
Contributor
Author
|
The build is clean except for two issues:
If we ignore the above two issues, which are independent of the code in this PR, the build is clean. |
abhishekrb19
reviewed
Apr 7, 2023
Contributor
 abhishekrb19
left a comment
abhishekrb19
left a comment
There was a problem hiding this comment.
Thanks for adding this @paul-rogers! The change overall looks good. I left some comments.
| ``` | ||
| An example configuration: | ||
|
|
||
| ```text |
Contributor
There was a problem hiding this comment.
nit: if you switch this from text -> properties, you get some nice syntax highlighting
Suggested change
| ```text | |
| ```properties |
| ``` | ||
| > Note: Druid treats the resource name as a regular expression (regex). You can use a specific datasource name or regex to grant permissions for multiple datasources at a time. | ||
| ] | ||
| ``` |
Contributor
|
|
||
| class BasicAuthClient: | ||
| ''' | ||
| Manage Basic security. The Druid session must be logged in with the super |
Contributor
There was a problem hiding this comment.
nit: "Basic" -> "basic"
| Returns both the authenticator and authorizer status. | ||
| ''' | ||
| return { | ||
| "authenticator": self.authorization_status(), |
Contributor
There was a problem hiding this comment.
Same as below - I think the status assignment for authenticator and authorizer is flipped.
| Returns the list of authenticator and authorizer users. | ||
| ''' | ||
| return { | ||
| "authenticator": self.authorization_users(), |
Contributor
There was a problem hiding this comment.
Should this be:
return {
"authenticator": self.authentication_users(),
"authorizer": self. authorization_users()
}| basic security enabled, you must specify the admin user and password: | ||
|
|
||
| ``` | ||
| coord = druidapi.jupyter_client('http://localhost:8081', auth=('admin', 'admin-pwd')) |
2 tasks
vtlim
added a commit
that referenced
this pull request
Apr 11, 2023
Contributor
|
This change was included in #14055 |
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
Sign up for free
to join this conversation on GitHub.
Already have an account?
Sign in to comment
Add this suggestion to a batch that can be applied as a single commit.This suggestion is invalid because no changes were made to the code.Suggestions cannot be applied while the pull request is closed.Suggestions cannot be applied while viewing a subset of changes.Only one suggestion per line can be applied in a batch.Add this suggestion to a batch that can be applied as a single commit.Applying suggestions on deleted lines is not supported.You must change the existing code in this line in order to create a valid suggestion.Outdated suggestions cannot be applied.This suggestion has been applied or marked resolved.Suggestions cannot be applied from pending reviews.Suggestions cannot be applied on multi-line comments.Suggestions cannot be applied while the pull request is queued to merge.Suggestion cannot be applied right now. Please check back later.
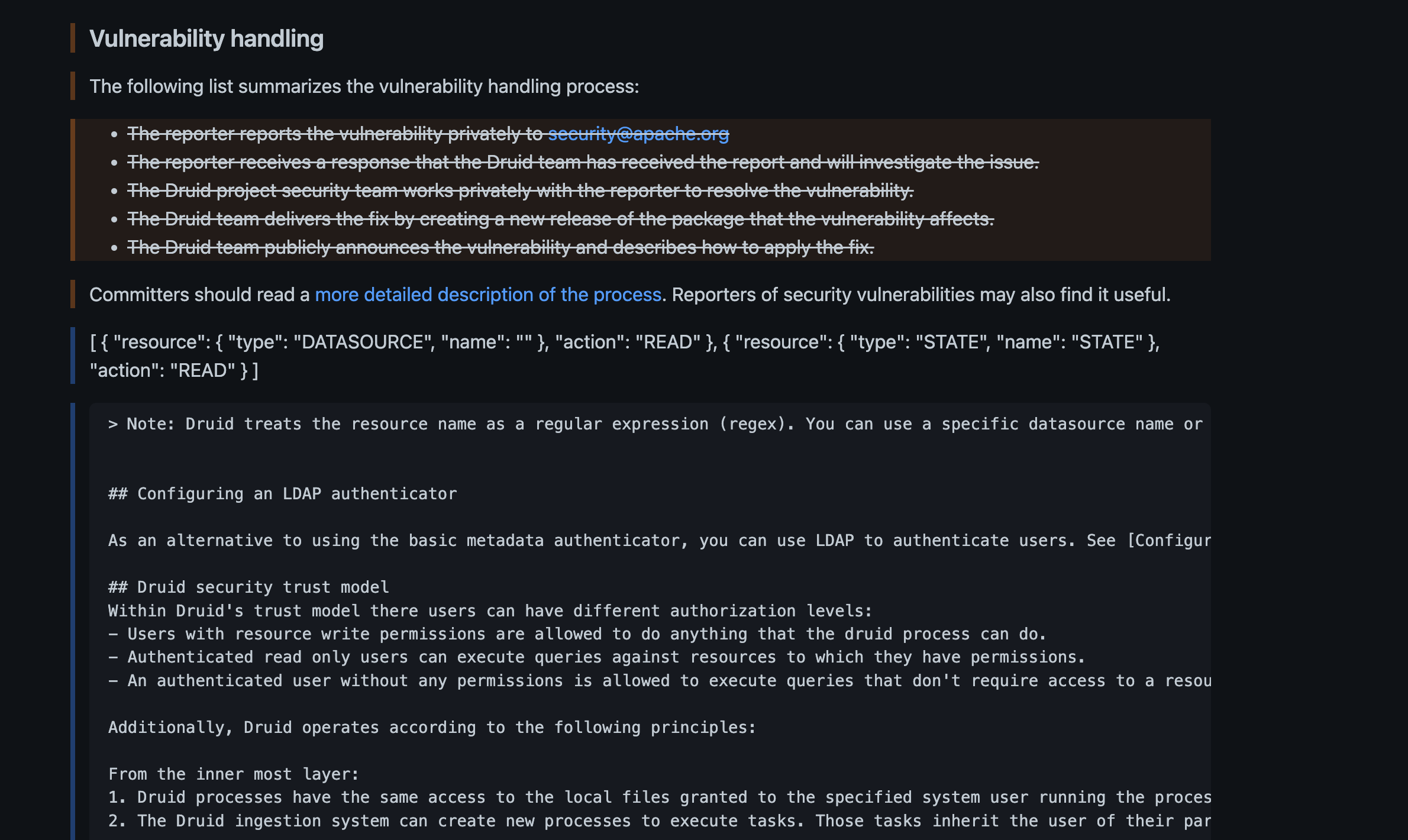
This PR adds a complete set of Basic security functions to the Python
druidapi. These functions are handy for setting up security, inspecting the security setup, and learning the nuances of the basic security system. They would make a fine foundation for Basic security tutorial notebook. If we did such a notebook:Since the Druid console doesn't provide tools to set up basic security, doing it via Python is a handy way to get started until a user defines a more production-grade integration with an external system.
Example:
Release note
See the description.
This PR has: