Conversation
|
@esbran Let's discuss whether the health bot also needs to be deployed here or whether we should treat this separately. I haven't seen any integration between the two, which is why the health bot could be treated separately. Depending on this and the next steps, I will either:
|
* adopted new repo structure
* added healthbot * updated main bicep to include new resources * added params
|
@esbran The Portal UI was added and can be used once the repo is public. |
…into healthcare_api
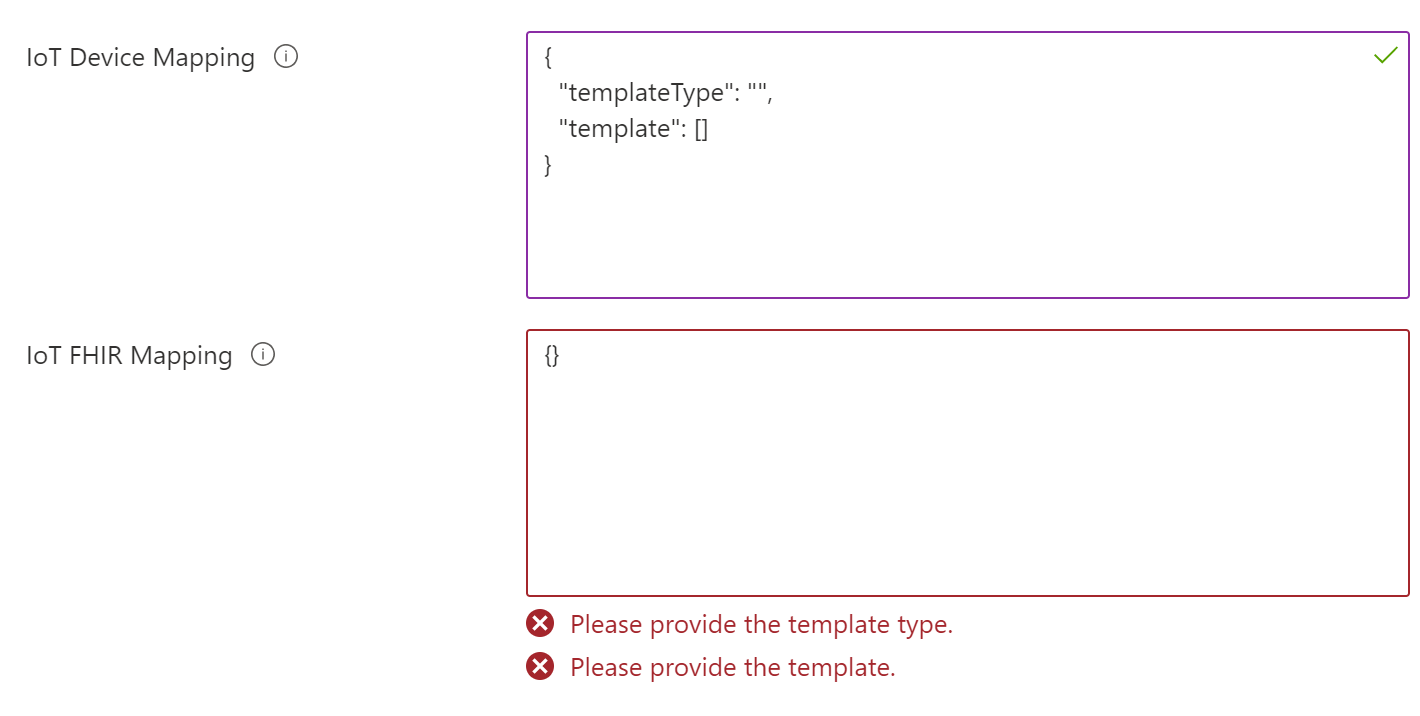
* added option to select between IoT Hub and EH in ARM * Added selection in portal * Added validation for mapping in portal
|
|
||
| Classical IoT as well as IoMT scenarios share similar architectures. The most significant differences can be identified on the application and data-driven use-case level. Also, there is a higher emphasis on the security aspect in the IoMT space and the compliance with legal regulations and standards. In the next paragraphs, we will look at the various layers of an IoMT architecture. | ||
|
|
||
| ## IoMT Architecture |
There was a problem hiding this comment.
This is great. I was also wondering (although knowing it's early stage) if we can lead with critical design areas for IoMT, and flush out some design considerations/recommendations across those? That should help to position the reference architecture and the rationale behind the composition and integration we are recommending. Thoughts?
There was a problem hiding this comment.
Can I work on this as part of a second iteration?
Would that work?
| "description": "Specifies the resource ID of the subnet to which all services will connect." | ||
| } | ||
| }, | ||
| "privateDnsZoneIdEventhubNamespace": { |
There was a problem hiding this comment.
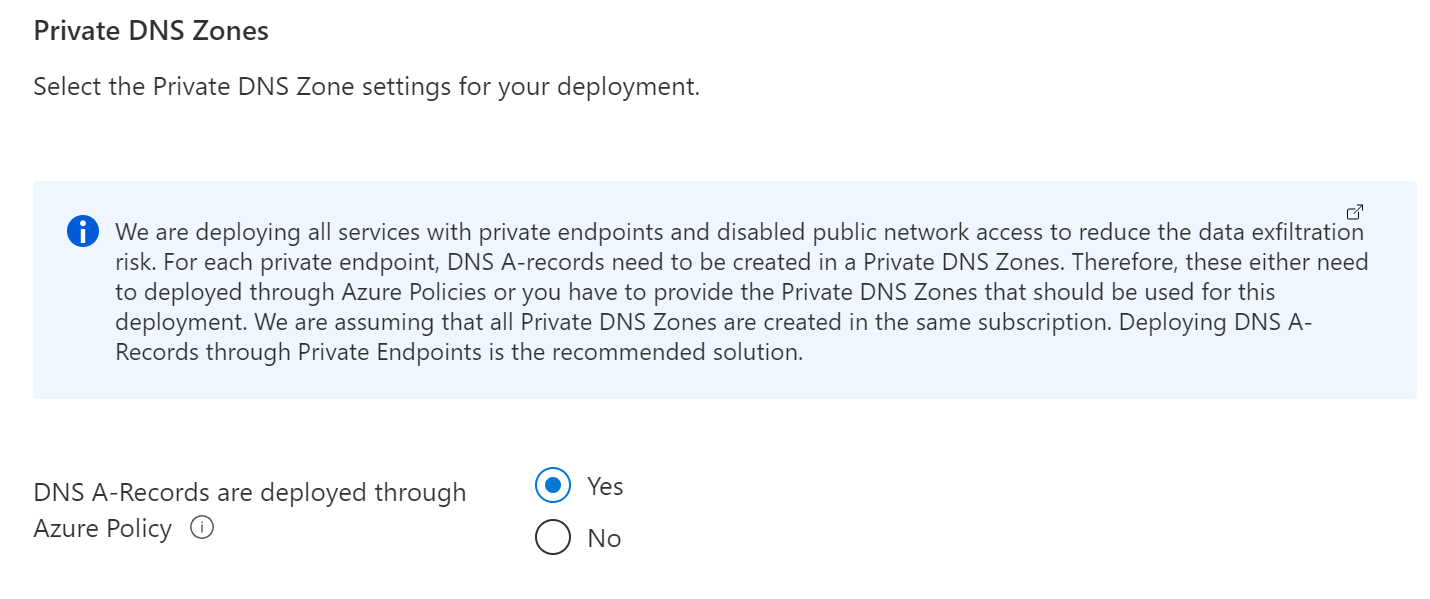
Assuming the ones who are deploying this will not have RBAC to the resourceId, could we call that out in the documentation that this 1) takes a dependency on platform networking, and 2) the recommended ways to achieve it?
Healthcare/solutions/IoMT/modules/services/eventhubnamespace.bicep
Outdated
Show resolved
Hide resolved
Healthcare/solutions/IoMT/modules/services/eventhubnamespace.bicep
Outdated
Show resolved
Hide resolved
|
I will close this soon due to some issues in history. Let's continue here: #46 |
* wave #1 * adding AKS * added defender options * adding mySql and other minor updates * update * backup completeness * update + event grid * adding Azure Data Explorer * minor update * adding rbac * formatting * adding ARM template for compliant services * v2 refresh * optimizing dependency * adding policies * dns update * Update hubspoke-connectivity.json * Update industryArmV2.json * Update hubspoke-connectivity.json * Update fsiPortalV2.json * Update industryArmV2.json * adding EH for data export * Compliant network policySet * prevent ssh and rdp from internet to network * erDiag * updated data export with description * adding sub for ingress and egress * adding assignments * name lenght * updated KV and adding cosmosDb * more data stuff * removing 'db' * compliant events * aks + nw * Update Cognitive Services Policies (#370) Co-authored-by: Kristian Nese <kristian.nese@microsoft.com> * nw part 1 * network orchestration * sql policySet * adding sql, service bus, and postgre sql * adding sql assignment + storage def and assignment * updating condition * lenght * correcting params * Network Policies (#374) * Network Policies * Removing duplicate assignments --------- Co-authored-by: Kristian Nese <kristian.nese@microsoft.com> * adding synapse * update assignment name * param mapping * compliant corp lz * update condition * fixing url * converge on private DNS across verticals * compliant corp lz and modification to each vertical * updated compliant services * adding AVD * Centralized logging initiative * added diag to storage account * naming convention for storage * default identity sub behavior * Add Azure Storage Policies (#375) * Add Azure Storage Policies * Fix minor bug * Update type * Add policy for CORS rules * Add policy for CMK for encryption scopes * Remove policy for encryption scope * Update display name * Add list of allowed values for policy definition * Update policy for encryption * Add policy assignments * Removed policy for cross tenant PEs * Add missing parameters * Update mg name * update sequencing --------- Co-authored-by: Marvin Buss <34542414+marvinbuss@users.noreply.github.com> Co-authored-by: Uday Pandya <14359777+uday31in@users.noreply.github.com>
* update platform resource config * updated default value for policydef * updated resourceNames for policy * adding udr and nsg to private dns * Allowed resourceTypes wave #1 * allowed corp resources + peering with udr and nsg * updated resource types and NW sequencing for ERGW
In this branch I am working on the IoMT scenario and templates to have a sample that can be used for such scenarios.
Added: