Security Build Definition#20873
Conversation
| "scriptName": "", | ||
| "arguments": "$(Build.SourcesDirectory) $(PB_CloudDropAccountName) $(PB_CloudDropAccessToken) $(PB_CloudDropContainer)", | ||
| "workingFolder": "$(Build.SourcesDirectory)", | ||
| "inlineScript": "param($SrcDir, $account, $token, $container)\n$syncCmd = Join-Path \"$SrcDir\" \"sync.cmd\"\n$p = Start-Process $syncCmd -ArgumentList \"-ab -- /p:CloudDropAccountName=$account /p:CloudDropAccessToken=$token /p:ContainerName=$container\" -PassThru -NoNewWindow -ErrorAction Stop -Wait -Verbose \nWrite-Host \"Exit Code: $($p.ExitCode)\"\n\n\n", |
There was a problem hiding this comment.
There's a lot of inline scripts, any reason these can't be done with BuildTools? #Resolved
There was a problem hiding this comment.
Please try this query - https://msazure.visualstudio.com/defaultcollection/One/_workitems?tempQueryId=f4c69d04-1a80-4fef-ad4b-8f0dd0a8af04 #Closed
There was a problem hiding this comment.
There's a lot of inline scripts, any reason these can't be done with BuildTools?
This particular script is simply running sync.cmd, which is similar to how other build definitions do. But for other inline scripts such as extract packages, yes, having something in BuildTools such as an MSBuild target that can be used cross-plat is better choice. I can log an issue to track that work. What do you guys say? #Closed
There was a problem hiding this comment.
Why do you need an inline script to run a command? Why not just run the command from a command window the same way a dev would? #Resolved
|
@ravimeda this looks like a good start. Some of the BinSkim issues suggest you need to fix a couple things:
Once you have those fixed up, it'll be easier to see whether there are any other issues needing action. What's your plan to suppress/baseline false positives, which there seem to be a lot of from CredScan and PoliCheck? #Resolved |
| "timeoutInMinutes": 0, | ||
| "condition": "succeeded()", | ||
| "task": { | ||
| "id": "3056813a-40e9-4b2f-8f6b-612d1bc4e045", |
There was a problem hiding this comment.
Do all these tools already have custom vsts tasks associated with them? #Resolved
There was a problem hiding this comment.
Yes, each tool has a custom VSTS task referred to as Security Extension. Details at http://aka.ms/sdtvsts #Resolved
|
Thanks @morganbr Couple comments -
@chcosta @dagood logged dotnet/buildtools#1565 to avoid custom PowerShell script to extract packages. |
|
@ravimeda , sounds good. When you have new BinSkim results, let me know and I'll take a look. #Resolved |
|
Cleared up the noise from test builds, and did a couple fresh builds. List of issues reported from these new builds is summarized in the table below:
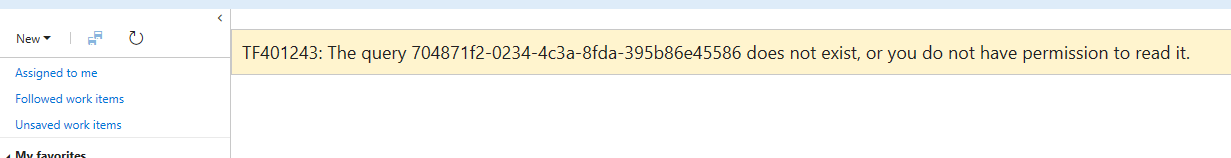
Full list of issues is at https://msazure.visualstudio.com/defaultcollection/One/_workitems?tempQueryId=94620dd6-d32e-4f1e-b2bb-1cf748f7dd51 Next steps on how we want to proceed with security builds:
Cc @dleeapho #Closed |
* Remove folders other than security. * Update args for BinSkim. * Cleanup scripts. * Fix APIScan args. * Update task names. * Update PB variable name. * Do delete .txt files. Version.txt is needed. * Set symbolsFolder for APIScan. * Update git checkout task. * Add a test task that will be removed before merge. * Add PB_Git variable. * Update Git path. * Revert to PB_Git. * Remove test task.
|
Adding @wtgodbe to take a look as well since he has been involved in related security efforts. |
* Create root and windows definition. * Include PB_ prefix. * Remove variables whose values will be in PB. * Remove unnecessary tasks. * Update path property. * Add OSX leg. * Remove triggers. * Remove PB variables. * Remove OSX leg since there is no TSA support. * Remove CodeMetrics. * Pass official build number as PB variable. * Invoke sync.cmd directly. * Update arguments passed to security tools. (dotnet/corefx#11) * Minor fixes to arguments passed, and variable names. (dotnet/corefx#12) * Remove folders other than security. * Update args for BinSkim. * Cleanup scripts. * Fix APIScan args. * Update task names. * Update PB variable name. * Do delete .txt files. Version.txt is needed. * Set symbolsFolder for APIScan. * Update git checkout task. * Add a test task that will be removed before merge. * Add PB_Git variable. * Update Git path. * Revert to PB_Git. * Remove test task. Commit migrated from dotnet/corefx@114dc02
Introducing build definition that will run security tools required to comply with Security Development Lifecycle (SDL). The build definition puts together VSTS extensions that run the tools, analyze logs, and upload results to Trust Services Automation that creates workitems for identified security issues.
List of tools included in this definition are:
Approach followed in this build is:
$(Build.SourcesDirectory)\securityRunning this build identified the following issues https://msazure.visualstudio.com/defaultcollection/One/_workitems?tempQueryId=f4c69d04-1a80-4fef-ad4b-8f0dd0a8af04
@morganbr @weshaggard @chcosta @dagood PTAL
Cc @gkhanna79
Edit 6/12: Described the approach for the build, and updated the query link.
Edit 6/12: Fixed type "Trust Services Automation"